In a previous blog post, I outlined how security procedures fit in an organization’s overall information security documentation library and how they provide the “how” when it comes to the consistent implementation of security controls in an organization. This blog post takes you back to the foundation of an organization’s security program – information security policies. It also covers why they are important to an organization’s overall security program and the importance of information security in the workplace. Before we dive into the details and purpose of information security policy, let’s take a brief look at information security itself.
What is Information Security?
Put succinctly, information security is the sum of the people, processes, and technology implemented within an organization to protect information assets. It also prevents unauthorized disclosure, disruption, access, use, modification, etc. of those information assets. There are three principles of Information security, or three primary tenants, called the CIA triad: confidentiality (C), integrity (I), and availability (A). They are defined as defined below:
Confidentiality — the protection of information against unauthorized disclosure
Integrity — the protection of information against unauthorized modification and ensuring the authenticity, accuracy, non-repudiation, and completeness of the information
Availability — the protection of information against unauthorized destruction and ensuring data is accessible when needed
Why is information security important? Without information security, an organization’s information assets, including any intellectual property, are susceptible to compromise or theft. As a result, consumer and shareholder confidence and reputation suffer potentially to the point of ruining the company altogether. It is important to keep the principles of the CIA triad in mind when developing corporate information security policies.
What is an Information Security Policy?
Put simply, an information security policy is a statement, or a collection of statements, designed to guide employees’ behavior with regard to the security of company information and IT systems, etc. These security policies support the CIA triad and define the who, what, and why regarding the desired behavior, and they play an important role in an organization’s overall security posture.

Why Do You Need an Information Security Policy?
The goal when writing an organizational information security policy is to provide relevant direction and value to the individuals within an organization with regard to security. While entire books have been published regarding how to write effective security policies, there are a few core reasons why your organization should have information security policies:
- Information security policies define what is required of an organization’s employees from a security perspective
- Information security policies reflect the risk appetite of an organization’s management and should reflect the managerial mindset when it comes to security
- Information security policies provide direction upon which a control framework can be built to secure the organization against external and internal threats
- Information security policies are a mechanism to support an organization’s legal and ethical responsibilities
- Information security policies are a mechanism to hold individuals accountable for compliance with expected behaviors with regard to information security
Below are a few principles to keep in mind when you’re ready to start tapping out (or reviewing existing) security policies.
What Should An Information Security Policy Include?
Since security policies should reflect the risk appetite of executive management in an organization, start with the defined risks in the organization. Write a policy that appropriately guides behavior to reduce the risk. If an organization has a risk regarding social engineering, then there should be a policy reflecting the behavior desired to reduce the risk of employees being socially engineered. One such policy would be that every employee must take yearly security awareness training (which includes social engineering tactics).
Since information security itself covers a wide range of topics, a company information security policy (or policies) are commonly written for a broad range of topics such as the following:
- Access control
- Identification and Authentication (including multi-factor authentication and passwords)
- Data classification
- Encryption
- Remote access
- Acceptable use
- Patching
- Malicious code protections
- Physical security
- Backups
- Server security (e.g. hardening)
- Employee on/offboarding
- Change management
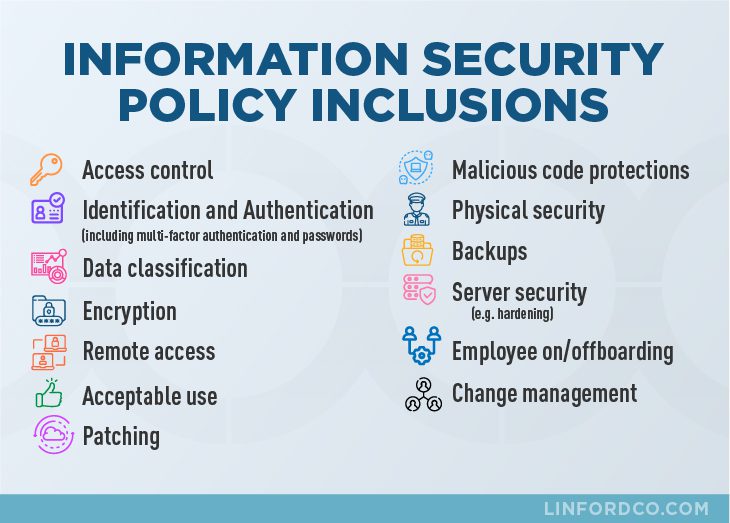
Note that the above list is just a sample of an organizational security policy (or policies). Compliance requirements also drive the need to develop security policies, but don’t write a policy just for the sake of having a policy.
What Should You Keep in Mind When Writing an Information Security Policy?
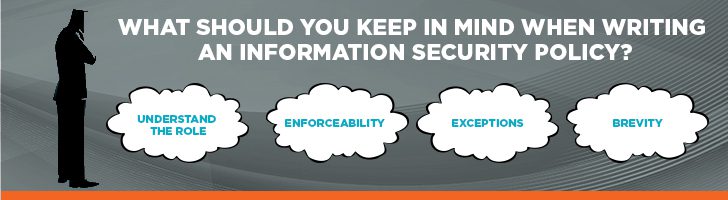
1. Understand the role of security policies in your organization
One of the primary purposes of a security policy is to provide protection – protection for your organization and for its employees. Security policies protect your organization’s critical information/intellectual property by clearly outlining employee responsibilities with regard to what information needs to be safeguarded and why. When the what and why is clearly communicated to the who (employees) then people can act accordingly as well as be held accountable for their actions. Employees are protected and should not fear reprisal as long as they are acting in accordance with defined security policies.
Another critical purpose of security policies is to support the mission of the organization. Security professionals need to be sensitive to the needs of the business, so when writing security policies, the mission of the organization should be at the forefront of your thoughts. Ask yourself, how does this policy support the mission of my organization? Is it addressing the concerns of senior leadership?
Of course, in order to answer these questions, you have to engage the senior leadership of your organization. What is their sensitivity toward security? If they are more sensitive in their approach to security, then the policies likely will reflect a more detailed definition of employee expectations. This approach will likely also require more resources to maintain and monitor the enforcement of the policies. A less sensitive approach to security will have less definition of employee expectations, require fewer resources to maintain and monitor policy enforcement, but will result in a greater risk to your organization’s intellectual assets/critical data.
Either way, do not write security policies in a vacuum. If you do, it will likely not align with the needs of your organization. Writing security policies is an iterative process and will require buy-in from executive management before it can be published.
2. Ensure your security policies are enforceable
If the policy is not going to be enforced, then why waste the time and resources writing it? It is important that everyone from the CEO down to the newest of employees comply with the policies. If upper management doesn’t comply with the security policies and the consequences of non-compliance with the policy is not enforced, then mistrust and apathy toward compliance with the policy can plague your organization.
Look across your organization. Can the policy be applied fairly to everyone? If not, rethink your policy. Security policies are supposed to be directive in nature and are intended to guide and govern employee behavior. If the policy is not enforced, then employee behavior is not directed into productive and secure computing practices which results in greater risk to your organization. Users need to be exposed to security policies several times before the message sinks in and they understand the “why” of the policy, so think about graduating the consequences of policy violation where appropriate.
Another important element of making security policies enforceable is to ensure that everyone reads and acknowledges the security policies (often via signing a statement thereto). Many security policies state that non-compliance with the policy can lead to administrative actions up to and including termination of employment, but if the employee does not acknowledge this statement, then the enforceability of the policy is weakened.

3. Explain how policy exceptions are handled
You’ve heard the expression, “there is an exception to every rule.” Well, the same perspective often goes for security policies. There are often legitimate reasons why an exception to a policy is needed. In these cases, the policy should define how approval for the exception to the policy is obtained. Management should be aware of exceptions to security policies as the exception to the policy could introduce risk that needs to be mitigated in another way.
4. Make your security policies brief and succinct
Security policies should not include everything but the kitchen sink. Supporting procedures, baselines, and guidelines can fill in the “how” and “when” of your policies. Each policy should address a specific topic (e.g. acceptable use, access control, etc.); it will make things easier to manage and maintain.
Keep it simple – don’t overburden your policies with technical jargon or legal terms. Use simple language; after all, you want your employees to understand the policy. When employees understand security policies, it will be easier for them to comply. When writing security policies, keep in mind that “complexity is the worst enemy of security” (Bruce Schneier), so keep it brief, clear, and to the point.

Why is it Important To Keep Security Policies Current?
The purpose of security policies is not to adorn the empty spaces of your bookshelf. Security policies can stale over time if they are not actively maintained. At a minimum, security policies should be reviewed yearly and updated as needed. It is good practice to have employees acknowledge receipt of and agree to abide by them on a yearly basis as well.
In preparation for this event, review the policies through the lens of changes your organization has undergone over the past year. What new threat vectors have come into the picture over the past year? What have you learned from the security incidents you experienced over the past year? Take these lessons learned and incorporate them into your policy. Security policies are living documents and need to be relevant to your organization at all times.
Summary
In this blog, we’ve discussed the importance of information security policies and how they provide an overall foundation for a good security program. With defined security policies, individuals will understand the who, what, and why regarding their organization’s security program, and organizational risk can be mitigated.
Linford and Company has extensive experience writing and providing guidance on security policies. If you would like to learn more about how Linford and Company can assist your organization in defining security policies or other services such as FedRAMP, HITRUST, SOC 1 or SOC 2 audits, please contact us.

Ray Dunham started his career as an Air Force Officer in 1996 in the field of Communications and Computer Systems. Following his time in the Air Force, Ray worked in the defense industry in areas of system architecture, system engineering, and primarily information security. Ray leads L&C’s FedRAMP practice but also supports SOC examinations. Ray enjoys working with clients to secure their environments and provide guidance on information security principles and practices.



