In this article, we will cover some common questions that come up related to SOC 2 reports. SOC 2 does not have to be difficult although, with some of the terminology, it can initially be confusing. So what are SOC 2 reports? Let’s dive in!
With today’s prevalence of cloud computing, information security and the security of sensitive data has never been more paramount. Around 90% of companies use some form of cloud computing and are trusting third parties like AWS, GCP, and Azure to protect sensitive data. Every day, new data breaches are reported, costing companies billions of dollars in combined losses. Reuters recently noted the global cost of a breach to be an average of 4.88 million dollars. In the US, the average cost is greater at 9.36 million dollars. Companies are playing catch-up with attackers, and in many cases have insufficient internal controls to identify breaches and mitigate the risk of a breach of customer data.
In the U.S., many information security regulations are sectoral and industry-specific (e.g., PCI DSS, HIPAA, NERC CIP). What that means is that these frameworks are focused on a specific industry or type of data. PCI is focused on cardholder data, HIPAA is focused on patient health information, and NERC CIP (North American Electric Reliability Corporation Critical Infrastructure Protection) is focused on the energy industry.
In the US, SOC 2 compliance is the closest we have to a general information security standard.
What is a SOC 2 Report?
So what exactly is a SOC 2 report? It is a report that service organizations receive and share with stakeholders to demonstrate that general IT and business internal controls are in place to secure the service provided. SOC 2 differs from some other information security standards and frameworks because there is not a comprehensive SOC 2 list of “thou shalt” requirements. Instead, the AICPA provides criteria that may be selected by a service organization for inclusion in their SOC 2 report to demonstrate they have controls in place and operating effectively to mitigate risks to the service they provide.
Recently we were performing a readiness assessment for a SOC 2 report and our client had outsourced system development to a third party. Our client said the third party had their own SOC 2 report and they showed it to us. We started to review the report together and we were shocked that the report did not include a CPA firm’s opinion on whether the SOC 2 criteria was met. There was an assertion provided by management that the controls were met, but no auditor’s opinion. Without the CPA firm’s opinion, the report is not a SOC 2. Our client’s vendor had assembled a “SOC 2” themselves and was passing it off as a legitimate SOC 2. Yikes.
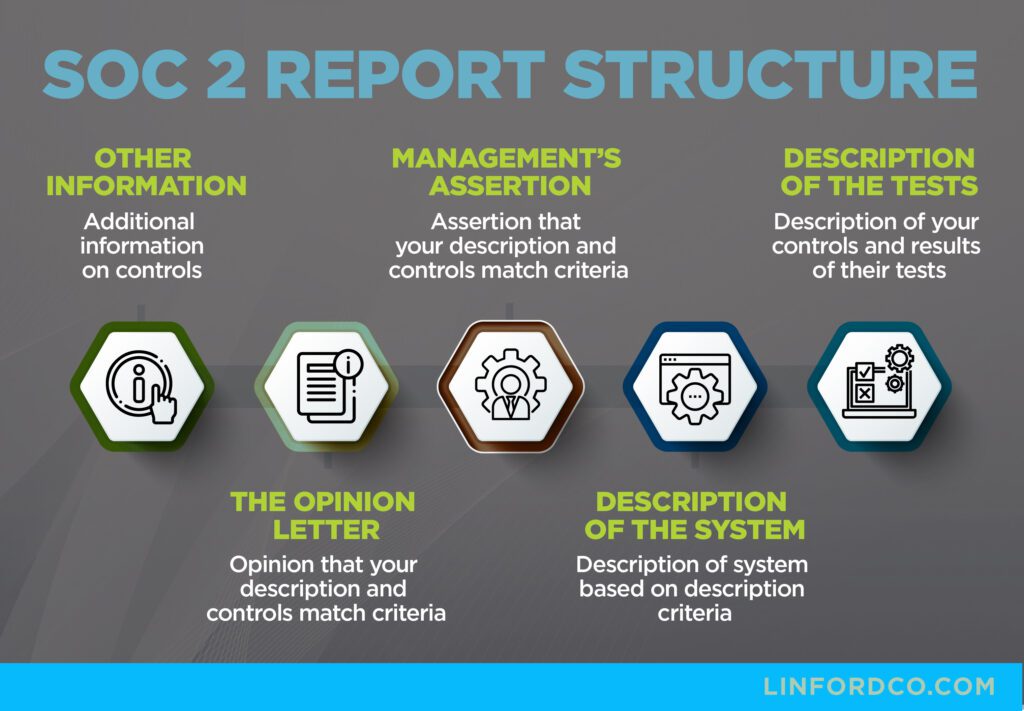
Required Components of a SOC 2 Report
- Independent Auditor’s Report (Opinion Letter)
-
- Conducted by an independent CPA (Certified Public Accountant).
- States whether the organization’s controls meet the required criteria.
- Includes an opinion (unqualified, qualified, adverse, or disclaimer of opinion) on the effectiveness of controls.
-
- A statement from the service organization’s management affirming that the controls were designed and implemented in alignment with the Trust Service Criteria (TSC).
- Declares that controls were in place for the audit period (for SOC 2 Type II).
- System Description
-
- A detailed overview of the system covered by the SOC 2 audit.
- Describes services, infrastructure, software, processes, and data handling.
- Helps stakeholders understand how the organization operates and protects information.
- Applicable Trust Service Criteria (TSC)
-
- Evaluates controls based on one or more of the following five TSC categories:
- Security – Protection against unauthorized access (mandatory for all SOC 2 reports).
- Availability – Ensures systems are operational and accessible as agreed.
- Processing Integrity – Ensures data is processed accurately and completely.
- Confidentiality – Protects sensitive business information.
- Privacy – Ensures the proper handling of personal information.
- Evaluates controls based on one or more of the following five TSC categories:
- Controls & Tests of Controls
-
- Lists the specific security controls implemented by the organization.
- Describes how auditors tested each control (e.g., interviews, document review, system testing).
- Includes test results and any exceptions or deficiencies found.
- Results of Testing
-
- Summarizes the effectiveness of controls during the audit period.
- Identifies any weaknesses or control failures, along with potential risks.
- Additional Information (Optional)
-
- The organization may include additional details such as planned remediation efforts, security policies, or future improvements.
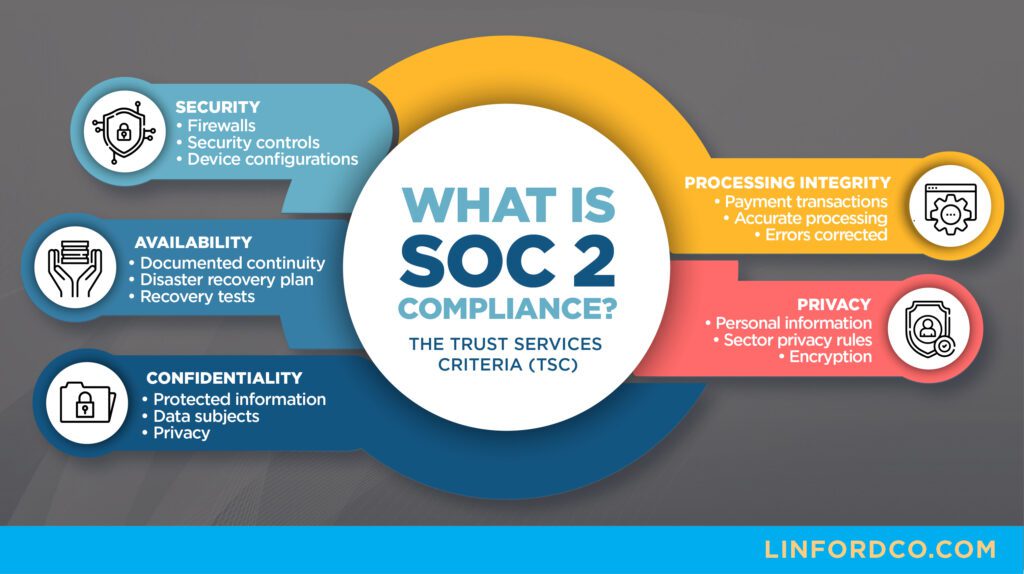
What Are the Trust Services Criteria (TSCs) Within a SOC 2 Report?
Trust Services Criteria (TSC) are the domains or scope covered in a SOC 2 report. Not all TSCs are required. In fact, only the common criteria are required (also referred to as the Security TSC). Other TSCs should be added to a report to answer common risk-related questions received from clients or to address risks facing the company and its unique service offering. For example, if the availability of healthcare data is extremely important to a service offering, then the availability criteria may be included in the SOC 2 report in addition to the security criteria.
We have had prospective clients say they wanted all of the TSCs included within their SOC 2 report because they wanted it to be the strongest report possible to demonstrate maximum compliance. While the logic makes sense, not all TSCs may apply to a particular client’s service. For example, if your company does not process transactions, processing integrity is probably not applicable.
We have heard of firms including TSCs when they are not applicable within a report and then explaining why they are not applicable within the report. That’s not advised. Your best bet is to select criteria that are applicable to your services and answer the risk-related questions you hear most from your clients and prospective clients.
When Should I Choose SOC 1 vs. SOC 2 vs. SOC 3?
Some companies struggle with the differences between SOC reports, and whether they should get a SOC 1, SOC 2, or SOC 3. We start by asking prospective clients about the type of clients and stakeholders asking for the report as well as the type of services provided to clients. This allows us to assess whether prospective clients may impact the internal controls over financial reporting (ICFR) of our prospective clients’ user organizations.
If a service organization can impact the ICFR of its user organizations, a SOC 1 report may be the best report option. If a service organization cannot impact its user organizations’ ICFR, but can impact the security, availability, processing integrity, confidentiality, or privacy of their user organizations, then a SOC 2 report may be the best report for the service organization’s clients. A SOC 3 report is a public-facing report usually used for marketing purposes that does not contain sensitive information that could be used as an attack vector for hackers.
What Does SOC 2 Compliance Mean?
A SOC 2 is a System and Organization Control 2 report. There are three types of SOC reports. See the AICPA website comparing the reports. Although a SOC 2 is technically an attestation report, it’s very common for people to call a SOC 2 a certification. It’s not a certification. See the AICPA page for more information, as well as this past blog post on qualified opinions. “SOC 2 compliance” or “SOC 2 compliant” are terms used to describe companies that are meeting one or more of the SOC 2 Trust Services Criteria. Each category of criteria has a number of requirements associated with it. For example, CC6.2 states:
Prior to issuing system credentials and granting system access, the entity registers and authorizes new internal and external users whose access is administered by the entity. For those users whose access is administered by the entity, user system credentials are removed when user access is no longer authorized.
This means that to comply with SOC 2 criteria CC6.2, a company must have a process grant system access to individuals who need it to perform their job duties. Companies could meet this requirement in a number of ways, including access provisioning and de-provisioning requests, role-based access guidelines, and greater levels of authorization for greater levels of access provisioned. SOC 2 criteria are worded generally, so the controls a company implements to meet each criterion could be unique to them.

What Is the Purpose of a SOC 2 Report?
A SOC 2 report shows stakeholders of service providers that they are following good security practices within their organization. In many cases, SOC 2s are required to do business with larger organizations such as financial institutions. Before a financial institution or other user organization will outsource a process to a service provider, they want to be sure that their client’s data will be adequately protected.
The trend towards cloud computing and outsourcing, in general, has fueled the need for SOC 2 reports in the U.S. SOC 2 compliance allows a service organization to provide assurance to its stakeholders that the service is being provided in a secure and reliable manner.
Learn more in our article, Leveraging the AWS SOC 2: How to Build a SOC 2 Compliant SaaS
How Does SOC 2 Compliance Ensure Data Security?
SOC 2 compliance does not ensure data security. There is no silver bullet to achieve data security. SOC 2 compliance means that an auditor has tested internal controls that meet the SOC 2 criteria covered in a SOC 2 examination. It is a general-use security analysis and demonstrates whether companies are achieving the basics with an information security program.

What Are the Benefits of SOC 2 Compliance?
SOC 2 compliance demonstrates that your company has adequate controls in place governing information security in your environment. A SOC 2 is stronger than giving your word that you are compliant since it’s an independent audit performed by a third-party CPA firm.
Listed below are a few reasons why companies choose to demonstrate SOC 2 compliance.
- Differentiate yourself from your competitors.
- Identify controls relevant to your clients and test those controls to validate the controls’ design and operation.
- Develop more controlled and consistent processes.
- In some cases, you can’t enter a particular market without a SOC 2. For example, if you are selling to financial institutions, they will almost certainly require a Type II SOC 2.
How Does SOC 2 Compliance Differ From Other Compliance Standards?
SOC 2 compliance requirements are general and not specific in nature. Other standards and frameworks such as PCI, HITRUST, FedRAMP, and ISO have more specific requirements. As a result, not all SOC 2 examinations cover the same set of controls. It’s up to an auditor working with a company to identify the most relevant controls in place to meet the relevant SOC 2 criteria.
Who Needs to Be SOC 2 Compliant?
Typically, service organizations that process or store sensitive data for their clients seek SOC 2 compliance. For example, many SaaS companies, data centers, and managed service providers. SOC 2 has been widely accepted as a U.S. standard for information security. As a result, some non-traditional service providers are demonstrating SOC 2 compliance, such as law firms, consultancies, and cryptocurrency services.

Other Common Questions About SOC 2 Compliance
The following are SOC 2-related questions that we hear often from clients.
Is There a SOC 2 Compliance Checklist or Shortcut?
There is no checklist, but the AICPA’s SOC 2 criteria can be obtained and reviewed. So how do you get it? You can buy it from the AICPA or contact us for a consultation. The criteria contains requirements related to each of the TSCs outlined above. The requirements may be met in a variety of ways, so there is not a one-size-fits-all checklist for SOC 2 compliance. It is dependent on the services provided by a service organization. The SOC 2 criteria also went through a recent update.
What Is SOC 2 Type 2?
SOC 2 can be Type 1 (aka Type I) or Type 2 (aka Type II).
Type I is dated as of a particular date and is sometimes referred to as “point-in-time”. Type I includes a description of a service organization’s system and a test of the design of the service organization’s relevant controls. Type I tests the design of a service organization’s controls, but not the operating effectiveness.
Type II covers a period of time (usually 12 months), includes a description of the service organization’s system, and tests the design and operating effectiveness of key internal controls over a period of time.
Who Needs a SOC 2 Report & Why?
Service organizations that provide a critical service to their clients or possess sensitive data belonging to their clients may need a SOC 2 report to demonstrate that they are taking the appropriate care to secure their environment and safeguard sensitive data.
How Long Does a SOC 2 Audit Take?
Several factors determine how long a SOC 2 audit might take. First, if you have strong internal controls already in place or if you have been through another compliance audit, that will certainly speed up the process. Some companies promise SOC 2 compliance in a short period of time (e.g. two weeks). While going through a SOC 2 audit in two weeks is possible, it’s not likely you could have a SOC 2 report in as little as two weeks because it takes time to complete the testing and issue the report. See our post related to how long it takes to get a SOC report.
Another factor is whether the audit firm has the availability to perform the audit. Some audit firms book up almost a year in advance and it takes time to make it on their schedule. There may also be competing priorities within the service organization. Approximately 40-80 hours may need to be dedicated to complete a first-year SOC 2 audit. If a service organization is heads down working on the product they are creating, a 40-80 hour impact may not be tolerable. Clients have to dedicate the time to complete the process, and if they can’t dedicate the time, that can slow things down.
How Often Are SOC 2 Reports Updated?
Type II SOC 2 reports are generally received on an annual basis and cover a twelve-month period. The first year some companies choose to receive a Type I SOC 2 since the report can be delivered faster generally (e.g. readiness assessment, remediation, issue Type I SOC 2). Also, some companies have to get a Type II SOC 2 for the first report to satisfy a client obligation or contract. In those cases, a company may choose to receive a report with a shorter examination period (e.g., readiness, remediation, wait six months, perform the SOC 2 audit).
How Can I Ensure My SOC 2 Report is Accurate?
It is up to both the audit firm performing the SOC 2 as well as the company receiving the SOC 2 to confirm the accuracy of the report prior to issuance. Potential issues should be confirmed by the auditor with the client and management before issuing the draft report. Management should read the report carefully and confirm both the language in Section III (process narratives), as well as the controls identified in Section IV, are accurate.
What Are the Consequences of Not Having a SOC 2 Report?
The main consequence of not having a SOC 2 report could be a loss of business and revenue for a service organization. Service organizations that do not have a SOC 2 report may not be able to do business with user organizations if they are in more regulated industries.
Also, security questionnaires can be long, and responding to them may start to take up too much of one person’s time. SOC 2s help when responding to user organization security queries and in some cases may be provided in place.
How Much Does a SOC 2 Examination Cost?
SOC 2 examinations are not cheap and fees depend on several factors. This includes the scope of services covered within the report, the TSCs included, the size of the organization, and the number of in-scope systems and processes.
For example, if a company has 3 different patch management processes to ensure servers and workstations stay up-to-date, the auditor will need to gain assurance that each of those processes is designed to operate effectively. Learn more in our article, How Much Does A SOC Audit Cost?
Lately, we have heard of other firms offering discounted fees for SOC 2 examinations that are as low as $5,000. Similar to many things in life, you get what you pay for. Are there actual auditors doing the work, or is AI being used to generate the report? Is the CPA firm specialized in performing SOC 2 audits, or do they have a CPA firm sign off on the reports that is disconnected from the actual work performed?
Who Will Be Held Accountable if There Are Inaccuracies in the SOC 2 Report?
It is up to both clients and their auditors to confirm the accuracy of the SOC 2 report prior to issuance. Different types of inaccuracies could make it into a SOC 2 report.
- One type is if the client overstates a control or provides evidence that is inaccurate to justify the performance of a control.
- Another type is if the audit firm doesn’t adequately understand the internal controls and processes that are in place. In that case, they could look at the wrong evidence in an attempt to test the control.
- A third type of inaccuracy in the report could be that the audit firm did not follow the appropriate AICPA guidance for compiling the report. That type of inaccuracy may be more difficult for a client to identify, but SOC audit firms are required to go through a peer review process every three years. This process includes reviewing a sample of reports, as well as the underlying evidence to confirm that the firm followed the appropriate guidance and there were no inaccuracies in reporting
Final Thoughts on SOC 2 Compliance & Reports
In summary, a SOC 2 is a report that a service organization receives related to Security, Availability, Confidentiality, Privacy, or Processing Integrity. All SOC 2s include the common criteria, which covers Security and then optionally may add additional criteria that are relevant to the service organization’s user organizations. SOC 2s are needed when a service organization provides a critical service to its customers and mistakes by the service organization could result in data breaches of sensitive information or loss of revenue.
If you have any questions related to SOC 2 reports, who needs them, or our firm’s process for completing a SOC 2 audit, please contact me to discuss.
This article was originally published on 11/22/2017 and was updated on 3/4/25.
Inquire About a SOC 2 Audit for Your Organization
Please use the form below to contact Rob Pierce for a free consultation to inquire about a SOC 2 audit for your organization.

Rob started with Linford & Co., LLP in 2011 and helps lead the HITRUST and ISO practices as well as performs SOC audits, NIST 800-171, and HIPAA assessments. He has spoken at Data Center World on compliance-related topics and has completed over 800 SOC examinations. He started his career as an IT auditor in 2003 with PwC in the Systems and Process Assurance group, and has worked in a variety of industries in internal audit as well as for the City and County of Denver.




