All SOC 2 examinations must include security common criteria. This includes reviewing a company’s (i.e., entity’s) risk assessment process (risks identified, risk matrix, controls in place to address the risks, etc.). However, one of the challenges that the AICPA has found when it comes to doing risk assessments is that companies are unclear on what the requirements are. In this week’s blog post, we will cover four common questions that play an important part in a risk assessment:
- What is a risk matrix?
- How do you create a risk matrix?
- What is a risk matrix used for?
- When to use and how to maintain a Risk Matrix.
Fundamental Overview of a Risk Assessment
Before we get into what a risk matrix is, we will start with a general overview of the steps involved in a risk assessment and where the risk matrix falls within the risk assessment lifecycle. Depending on which risk assessment methodology/framework a company elects to use (e.g., NIST SP 800-30, ISACA’s Risk IT, Carnegie Mellon’s OCTAVE, etc.), there may be a slightly different set of steps to follow as part of their risk assessment process. However, risk assessment frameworks generally cover the following four steps:
- Identify risks
- Analyze risks
- Address risks
- Monitor risks
When identifying risks, a risk assessment team should begin by considering the company’s overall objectives, the IT systems that support those objectives, and those systems’ underlying data. The team will want to ask those involved in the risk assessment process about the internal and external threats that exist; specifically, what do they think could cause an adverse effect on the company’s objectives and assets’ security, confidentiality, availability, processing integrity, and/or privacy?
In addition to threats, the risk assessment team will also want to consider the various vulnerabilities that exist in the company’s objectives and IT assets. Vulnerability considerations may include the underlying assets’ infrastructure, the systems themselves, their operating systems, their physical environment, and/or supply chain vulnerabilities from upstream service providers.
After the risks have been identified, the risk assessment team can move on to step two: analyzing the risks. The AICPA’s common criteria 3.2 (which aligns with COSO principle 7) states that as part of an entity’s controls around a risk assessment, “The entity identifies risks to the achievement of its objectives across the entity and analyzes risks as a basis for determining how the risks should be managed.” So, how does a company go about analyzing its identified risks?
The answer to this question can be found in the AICPA’s trust services criteria, where an additional point of focus explains what an entity needs to consider when analyzing each risk: “Considers the Significance of the Risk — The entity’s consideration of the potential significance of the identified risks includes (1) determining the criticality of identified assets in meeting objectives; (2) assessing the impact of identified threats and vulnerabilities in meeting objectives; (3) assessing the likelihood of identified threats; and (4) determining the risk associated with assets based on asset criticality, threat impact, and likelihood.” Steps 2 (impact) and 3 (likelihood) are where the risk matrix comes in.

What is a Risk Matrix & How Does One Work?
A risk matrix — sometimes called a risk rating matrix or risk control matrix — is a tool used to visualize and prioritize risks based on likelihood and impact. Whether you’re preparing for an audit, managing vendor relationships, or building an internal control framework, a risk matrix chart helps turn abstract threats into concrete action.
A risk matrix plots both the impact and likelihood levels of each identified risk so a company can arrive at an overall risk rating/level. Just as there are different risk assessment frameworks a company can choose to follow, a risk matrix can have multiple levels of impact and likelihood, along with different naming conventions. Let’s look at an example set of risk impact levels from NIST SP 800-30:
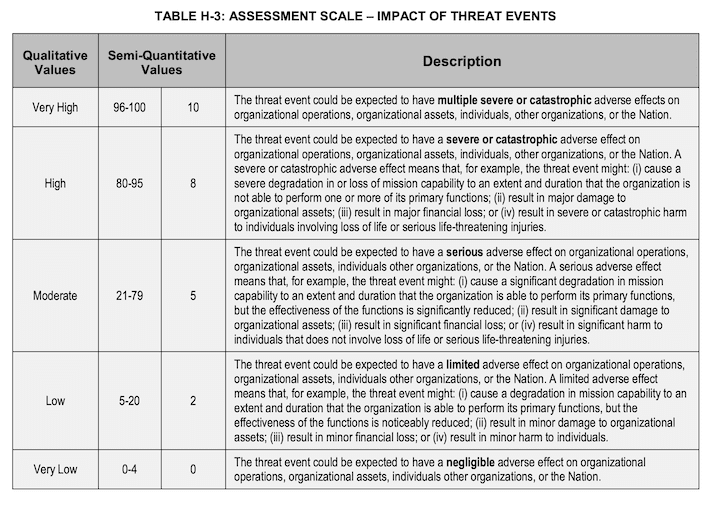
While NIST 800-30 defines five different impact levels, the qualitative naming convention, quantitative numbering scales, and descriptions can vary, depending on the risk assessment methodology used and each company’s needs. One entity may choose to use a simpler, three-level approach (high, medium, and low) while another company may opt to use nine impact levels. Regardless of how detailed an entity decides to document its risk impacts, the levels of impact should be clearly defined to ensure consistency in impact ratings across those who are involved in the risk assessment and rating process.
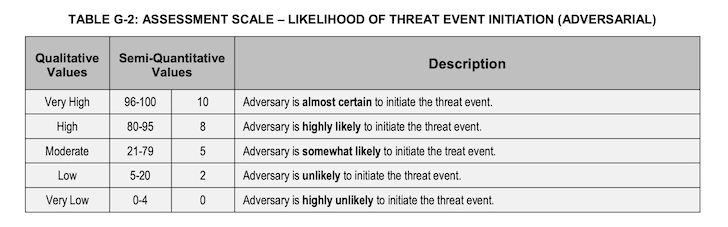
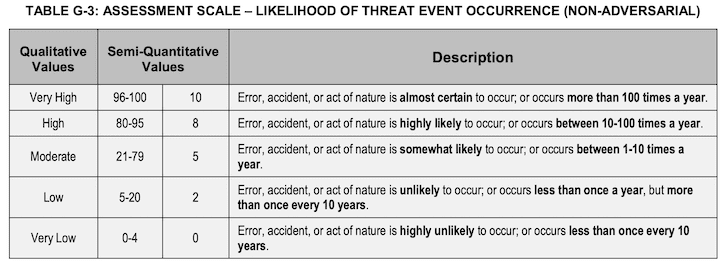
Once the impact has been defined, likelihoods should follow a similar approach of determining how many levels the entity will use and clearly defining what each likelihood level means. NIST provides another example of likelihood values (both qualitative and quantitative) and related descriptions:
How to Create a Risk Matrix
Now that risks have been identified and impacts and likelihoods defined, the risk matrix can be created. As with any part of the risk assessment process, the final risk levels and naming conventions may vary, depending on the entity’s definitions. Take a look at the risk matrix examples from NIST below.
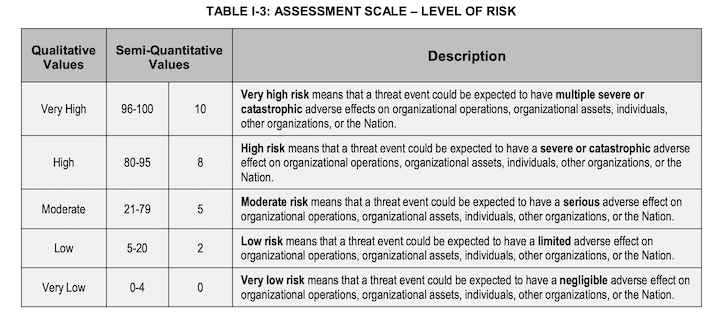
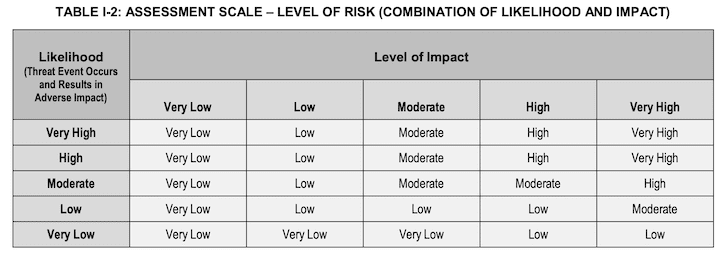
Even if the likelihood of a risk occurring is very high, but the impact is very low, the overall risk matrix specifies the risk to be very low. While that may be true for one company’s objectives, IT assets, and related data, it may not be true for another company. The entity’s final risk matrix, including definitions/descriptions of each risk level, is what will help those involved in the risk assessment process determine the final risk level of each identified risk.
What Do You Use a Risk Matrix For?
Because companies have limited time, people, and resources, a risk matrix helps senior management prioritize which risks warrant attention based on the organization’s risk tolerance. High-risk tolerance may mean accepting low or medium risks with minimal response, while lower tolerance might justify implementing some level of detective, preventative, compensating, and/or corrective controls for their medium and low-level risks. The value of a risk matrix is that it provides senior management with an easy illustration to review, understand, and start making decisions on how to proceed with the third step in the risk assessment process: addressing risk.
Doing all of this work to arrive at a decision-making tool is helpful to the team leading the risk assessment, but there is still more value that the risk matrix can provide. A risk matrix can also be used in the last phase of the risk assessment lifecycle (monitoring risks) by taking the original risk matrix that management used to prioritize which risks to address and updating it after controls have been put in place to address those risks. This type of monitoring, or comparison, focuses on what are called inherent and residual risks. Inherent risk is the level of risk that exists if the company does nothing to address the risk. Residual risk is the level of risk that exists after the company addresses the risk by allocating resources and time by implementing controls to lower the inherent risk. To learn more about inherent risk, read our article on inherent risk vs control risk.
Using a before-and-after snapshot of the risk matrix can be used to report the benefits of performing the risk assessment and implementing controls to senior management. For example, if a risk had been identified and rated to be a very high risk before any controls had been implemented, but subsequently the company addressed the risk by implementing controls to reduce the likelihood and/or impact of that risk (thus lowering the overall risk level) the result may be that the residual risk was reduced to a moderate level that is more aligned with the company’s risk tolerance level.

When to Use & How to Maintain a Risk Matrix
A risk assessment matrix can be used in a wide range of situations where risk-based decision-making is critical. Teams often build a risk matrix chart during early project planning, before launching new software features, or as part of vendor onboarding and evaluation. In regulated industries, organizations use a risk control matrix to satisfy requirements from frameworks like SOC 2, ISO 27001, or HIPAA by demonstrating that they have assessed and prioritized their operational and cybersecurity risks. For example, a risk management matrix can help identify and rank threats such as third-party data exposure, service downtime, or internal fraud. Whether you’re preparing for an audit or building a proactive security program, using a structured risk table allows teams to take informed, consistent action based on likelihood and impact.
A risk assessment matrix is not a one-time exercise — it should be treated as a living document that evolves with your business, systems, and threat landscape. Maintaining your risk matrix regularly ensures that it reflects current operations, control effectiveness, and emerging risks. Organizations that use a dynamic risk control matrix are better positioned to meet compliance expectations and respond swiftly to changes in vendor posture, internal processes, or external threats.
Key considerations for maintaining your risk matrix:
- Reassess risk ratings quarterly or after major business changes
- Assign owners to individual risks and control actions
- Monitor control performance to adjust likelihood/impact values
- Include fraud, insider threats, and vendor risks as standard entries
- Align matrix entries with your compliance framework (e.g., SOC 2 TSC, ISO 27001 Annex A)
- Leverage automation or GRC tools for continuous risk scoring and documentation
Common Risk Matrix FAQs
Below are common questions and answers to help you confidently integrate a Risk Matrix into your broader risk and compliance strategy.
What’s the Difference Between a Risk Assessment Matrix & a Risk Control Matrix?
A risk assessment matrix is a visual tool used to rank and prioritize risks based on their likelihood and impact. A risk control matrix, on the other hand, maps identified risks to specific controls — such as preventative, detective, or corrective measures — and often includes ownership, frequency, and evidence requirements for audits or compliance. Both tools are often used together in risk management programs.
How Often Should I Update My Risk Matrix?
Your risk rating matrix should be updated at least quarterly or whenever there’s a significant change to your systems, vendors, organizational structure, or regulatory requirements. Treat it as a living document — regular updates ensure it reflects your current risk landscape and keeps your mitigation strategies aligned.
Can I Use a Risk Matrix for Cybersecurity & Vendor Risk Management?
Yes. A risk analysis matrix is ideal for visualizing cyber risks such as unauthorized access, data breaches, or service downtime. It’s also commonly used to evaluate third-party vendors by mapping potential risks (e.g., insufficient encryption, poor access controls) to business impact and response urgency.
What Types of Risks Should Be Included in a Risk Matrix to Address SOC 2 Requirements?
To meet SOC 2 requirements, your risk assessment matrix should reflect the risks most relevant to the Trust Services Criteria (TSC) in scope for your audit. All SOC 2 reports must include Security (Common Criteria), while Availability, Processing Integrity, Confidentiality, and Privacy are optional depending on your organization’s services and commitments.
Your matrix should assess risks that could affect your ability to meet the selected TSC. Below is a mapping of typical risk types to their corresponding criteria.
The scope of your risk matrix should align with the TSCs selected for your SOC 2 engagement, ensuring that each relevant control area is supported by documented, evaluated, and prioritized risks. This approach supports the auditor’s expectations under CC3.2 and CC3.3, which require a formal, documented risk assessment process.
Key Takeaways: Implementing Your Risk Matrix Strategy
We covered what a risk matrix is (impact and likelihood), how to create one (defining various levels of impacts, likelihoods, and overall risks), and how a risk matrix can be used throughout the risk assessment lifecycle. Creating a risk matrix provides senior management with an illustration to be able to quickly and easily understand risks to the company’s objectives and make decisions on which risks to address.
If you are considering a SOC 2 examination, performing a risk assessment is a key element that will be covered during the audit. If you have any questions about the SOC 2 audit services offered by Linford & Co or the risk assessment trust services criteria, please contact us.
This article was originally published on 10/19/2022 and was updated on 7/9/2025.

Fred is an accomplished Information Technology consulting professional with 14+ years of experience in cyber security compliance audits. Fred is currently responsible for managing SOC 1 and SOC 2, ISO 27001 and HITRUST engagements across the United States for mostly SaaS companies. He started his career at Deloitte in their Enterprise Risk Services practice. Fred has served as a board member for his local ISACA chapter and holds current CISA and CISSP certifications.




