The designated roles and responsibilities of an Information security team can vary from organization to organization. These roles and responsibilities can vary depending on the service organizations size, structure, and business processes. With that being said, the following universal truisms should apply across all service organizations looking to implement an information security team structure:
- Individual roles, responsibilities, and authority are clearly defined, communicated, and understood by all stakeholders.
- The organization assigns and communicates security-related functions to designated employees.
To further expand on the importance of the information security team structure in your organization, this article will walk through examples of standard information security team roles and responsibilities, the importance of having documented job descriptions for these roles, and the purpose of implementing a clearly defined organizational chart that graphically depicts your information security team structure.

Information Security: Organization Structure, Roles, and Responsibilities
As stated above, it is imperative that individual roles, responsibilities, and authority are clearly communicated and understood by all, and that an organization assigns and communicates security-related functions to designated employees or order for an organization to have a successfully performing information security team. These requirements and others are outlined in the AICPA’s Trust Services Principles governing SOC 2 audit reports.
The following (below) is an example outline of various functional roles and associated responsibilities that make up and can help a new organization develop a standard information security team structure.
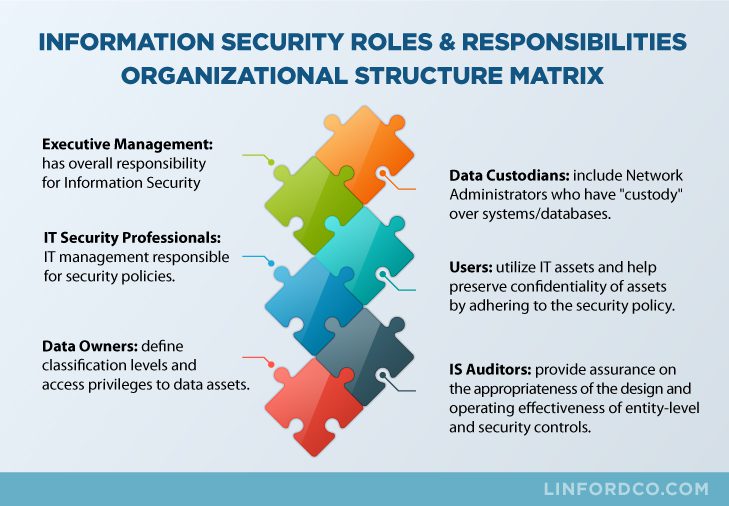
- Executive Management: Assigned overall responsibility for information security and should include specific organizational roles such as the CISO (Chief Information Security Officer), CTO (Chief Technology Officer), CRO (Chief Risk Officer), CSO (Chief Security Officer), etc. These executive level roles generally are responsible for overseeing the enterprise information security strategy that ensures information assets are protected.
- Information System Security Professionals:Responsible for the design, implementation, management, and review of the organization’s security policies, standards, baselines, procedures, and guidelines. Examples of these roles can include but are not limited to the following: IT security manager, IT Risk management manager, Compliance manager, IT security analyst, etc.
- Data Owners: Owners (data owners, information owner, system owners who have budgetary authority); responsible for:
- Ensuring that appropriate security—consistent with the organization’s security policy—is implemented in their information systems
- Determining appropriate sensitivity or classification levels
- Determining access privileges
- Data Custodians: A function that has “custody” of the system/databases, not necessarily belonging to them, for any period of time. Usually network administration or operations (those who normally operate the systems for the owners).
- Users: Responsible for using resources and preserving availability, integrity, and confidentiality of assets; responsible for adhering to security policy.
- IS Auditors: Responsible for:
- Providing independent assurance to management on the appropriateness of the security objectives
- Determining whether the security policy, standards, baselines, procedures, and guidelines are appropriate and effective to comply with the organization’s security objectives
- Identifying whether the objectives and controls are being achieved

The Importance of Job Descriptions for the Information Security Team Structure
Documented job descriptions are critical to ensure employees understand their roles and responsibilities pertaining to day-to-day operations. Further, a signed acknowledgment of job responsibilities should typically be required at the start of employment to ensure employees understand, acknowledge, and are held accountable for their roles within the organization — all of which helps strengthen an organization’s overall internal control environment.
Further, not only should security job descriptions be documented and known to key personnel, but they should be updated as needed and often reinforced. This will allow management to accurately set performance measures, incentives, and/or other rewards appropriate for responsibilities in the organization reflecting appropriate conduct and performance.
Lastly, properly documented security role job descriptions strongly influence the design of your internal control framework and increase the likelihood that they will operate effectively.

What is an Information Security Organizational Chart and How is it Used?
A clearly defined organizational chart should outline the structure of an organization’s staff, typically starting with an outline of the C-level staff, followed by the structure of those that report into those C-level roles. The purpose of this chart is to create a straightforward depiction of an organization’s hierarchy, which allows employees to understand lines of authority, relationships between other individuals in the organization, and who they need to report to when issues arise.
Organizational charts can outline the reporting structure and hierarchy of an entire organization, or they can be developed for individual functional teams, which would typically occur in mid to large organizations. An example of a functional team organizational chart would be one that is developed specifically to outline an Information Security team structure.
Lastly, an organizational chart should be a “living” and “breathing” document, meaning that it should be updated when headcount changes, and/or when roles are shifted, in order for it to be an accurate resource of reference.
Summary
In summary, when structuring your information security team, by starting with outlining the information security roles and responsibilities based on your organizational size, structure, and business processes, this will help direct the implementation and documentation of appropriate job descriptions and organizational charts. All of this activity is important to help ensure individuals are held accountable for their internal control responsibilities which will greatly contribute to strengthening your organizations overall internal control framework and ultimately achieving your organization’s strategic objectives.
Further, the information discussed in this blog covers just a few of the many aspects of developing a sound internal control environment for your organization. Linford and Company has extensive experience working with organizations to define their control environment. Please review our auditing services and contact us if you would like to learn more about how we can help you with your audit needs.








