If you were asked what every company or organization has in common, what would you say? Well, there are many potential answers, but one thing is for certain — all companies/organizations are at risk for internal cyber security threats. There is a lot of attention in the media about companies being hacked by external parties (e.g. individuals, criminal organizations, or nation-states), but the greater risk to organizations comes from those already within the “walls of the castle.”
What is Insider Threat?
On the surface, defining insider threat seems self-explanatory–a source of potential danger or harm to an organization stemming from someone that is within or part of an organization. There are, however, varied sources and motivations of insider threat.
Insider Threat Report: Ponemon Institute
In its 2022 Cost of Insider Threats Global Report, the Ponemon Institute provided interesting insider threat statistics regarding the costs of insider threats to organizations around the globe across 278 separate organizations. For the purposes of the report, insider threats were comprised of the following:
- Careless or negligent employees or contractors
- Criminal or malicious insider threat
- A credential thief
There are, of course, more fine-grained categorizations of insider threats, but the Ponemon report kept it simple.
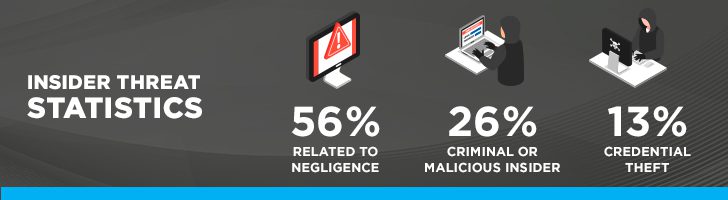
Insider Threat Statistics
As part of the Ponemon report, 1,004 security practitioners working in 278 organizations across the world were interviewed regarding the impact of insider threats on their organizations. Each of the 278 organizations had at least one material event caused by an insider, but there was a total of 6,803 insider incidents evaluated as part of the report. Of the 6,803 insider incidents evaluated, 56% were related to negligence, 26% resulted from a criminal or malicious insider, and 18% resulted from credential theft. The report also indicated that companies are spending an average of 85 days to contain a single insider security incident.
What are Examples of Insider Threats?
Examples of insider threats are wide and varied, but some of the more prevalent examples are outlined below:
- Theft of sensitive data. For many organizations, their trade secrets are their crown jewels that potentially represent decades of development and financial investment. This data is a target for the criminal or malicious insider who will attempt to exfiltrate and sell the data to competitors (potentially as a part of a new employment offer) or foreign governments.
- Induce downtime. You’ve heard the phrase “time is money.” This saying is especially true in today’s age of digital commerce. For companies that make millions by the minute, any downtime can be quite expensive, but downtime can also be detrimental to companies that have Service Level Agreements (SLA) with their clients. Violating an SLA due to downtime caused by an insider may put the company in jeopardy of losing a significant client or paying fees related to violation of the SLA.
- Destruction of property. While the destruction of physical property is less common than other insider attacks such as exfiltration of sensitive data, depending on the extent of the destruction, this specific risk may result in significant downtime and financial expenditures to replace damaged assets.
- Damage to reputation. Companies expend significant resources (i.e., time and money) to build and protect their brand. Within minutes (or less) a malicious insider attack can cause investors and clients to lose confidence in an organization’s ability to protect personal information, trade secrets, or other critical data. A loss of confidence often results in a loss of market share which results in a loss of revenue.

What are the Financial Impacts of Insider Threats?
Ultimately, though, each of the above risks impacts an organization financially. In their study, the Ponemon Institute also evaluated the financial impacts resulting from insider incidents.
In their research, the Ponemon Institute found that, on a per-incident basis, the costliest incidents were those involving credential theft which was more than double the cost per incident of those involving employee or contractor negligence, despite negligence being the most prevalent cause of insider threat. According to the report, the average number of credential thefts has increased significantly since 2018. In addition, the average current cost for remediating credential theft incidents is $804,997.
In terms of average annualized cost, though, employee and contractor negligence is the most costly to organizations.

What Are Some Potential Insider Threat Indicators?
Insider threat indicators can be categorized in various ways, but the Center for Development of Security Excellence groups insider threat indicators into three categories:
- Ignorance: Indicators in this category include clicking on a phishing scam, having a lack of awareness of security policies and unknowingly violating them, and not protecting passwords (or I would add having weak passwords).
- Complacency: Indicators in this category include uploading sensitive information to a third-party site and using personal devices to conduct company business without authorization.
- Malice: Malicious insider threat indicators include attempting to access data for which you are not authorized, stealing sensitive information, attempting to obtain passwords of co-workers, blatant disregard for security policies and practices.
Other insider threat indicators include disgruntled employees, employees performing activities outside of normal working hours, and large file transfers.
How Can Insider Threats Be Mitigated?
A good place to start when determining how to mitigate the risks of insider threats is to do an insider threat risk assessment. As part of the risk assessment, focus on the behaviors that indicate an insider attack. Once these behaviors are identified, then develop controls to support insider threat detection and prevention. Below are several suggestions regarding controls for detection and prevention:
Insider Threat Detection
- Implement a Data Loss Prevention (DLP) solution. DLP solutions detect potential cases of unauthorized access to data or attempts to exfiltrate or destroy sensitive data and alert staff to address attacks against sensitive corporate data. The first step in an effective DLP program is to identify sensitive data within the organization. Once identified, DLP rules can be most effectively applied.
- Configure auditing across the entire environment. Auditing is a critical capability that is often overlooked entirely or marginally implemented thus inhibiting an organization’s efforts to detect malicious or negligent insider activity. Once auditing is configured though, there must be mechanisms in place (e.g. SIEM) to assist with the analysis, correlation, and alerting on events of interest. The data must also be secured from tampering or deletion. Just having volumes of audit data without a means of analysis and alerting minimizes the value of the audit data as breaches or insider incidents may occur and be recorded, but an organization is blind to the malicious activity.
- Implement a Privileged Access Management (PAM) solution. While there are a lot of prevention capabilities within PAM solutions, they also offer detection capabilities such as session recording and auditing. This capability will record all activities (e.g. issued commands) performed by privileged users.
Preventing Insider Threats/Insider Threat Best Practices
- Implement DLP. Insider threats are a common cause of data leaks. In addition to the detection of potential insider threats, DLP technologies help organizations avoid and prevent the loss of sensitive data on their network. According to the Ponemon report, DLP solutions resulted in the greatest cost reductions (64%) due to insider threats.
- Limit privileged access. If at all possible, limit giving all privileged access across your organization to a single individual. Insider incidents from privileged users are especially nasty, so separate privileged responsibilities across multiple privileged users. Implement technical controls to limit privileges to only that which is necessary for the individual’s privileged role. For example, strictly limit who has access to the root user’s password and implement capabilities like “sudo” (in Linux) to define specific privileged commands that can be executed and limit who can modify the sudoers file. Another option, as mentioned previously, is to implement PAM, which enables very fine-grained administrative privileges. PAM solutions were cited in the Ponemon report as reducing the costs of insider risks by 60%.
- Implement User and Entity Behavior Analytics (UEBA). UEBA solutions monitor user behavior and identify activities that deviate from what is considered the norm. UEBA is commonly used to detect unauthorized data access as well as unauthorized data movement. Using machine learning, UEBA solutions analyze activity data from network users, hosts, applications, network traffic, data storage repositories, etc. UEBA solutions were credited with reducing the costs of insider risk by 57%, according to the Ponemon report.
- Segregate duties. This is especially difficult in smaller organizations where individuals wear many hats. That said, there must be controls in place to safeguard the organization from insider threats. Where possible, split administrative duties between competent staff members (remember negligence is a big factor in insider threats). We’ve seen small organizations rotate privileged access to their production environment to individuals for a week at a time while they rotate into DevOps roles for the week and then back their primary responsibilities in development.
- Block access to cloud storage sites. Sites such as Dropbox, Box, iCloud, OneDrive, Sync, and other cloud storage sites are a potential vector to easily exfiltrate corporate data. If these sites aren’t used by your organization, then block access to them.
- Implement Multi-factor Authentication (MFA). Implement MFA to mitigate the risk of credential theft. From my perspective, MFA should be implemented everywhere possible within an organization, but especially for privileged users. Read here for additional guidance on password policy guidelines.
- Limit access to sensitive data. All data within an organization should be categorized and protected in accordance with the associated categorization. It is important to know where sensitive data resides, who accesses it, and how it is accessed. Restrict access to corporate data to only those that require it to perform their job functions. In addition to limiting the access to data, use a DLP solution to tag and track data to determine who is accessing or downloading sensitive corporate data.
- Encrypt sensitive data. Encrypting sensitive data will provide protection if the data is successfully exfiltrated. Ensure that access to keys to decrypt the data are protected appropriately. Read here to learn more about why encryption is necessary.
- Back up your data. Ensure that critical data is frequently backed up to multiple locations and can be retrieved and restored. Having backups of critical data will come in handy when a malicious insider attempts to delete it in retaliation for being terminated or because they are angry. Access to backups should also be controlled to prevent deletion in addition to the critical data. In addition, develop procedures that outline how to restore data from backup.
Summary
Insider threats in cybersecurity are a significant risk to organizations, and according to the Ponemon Institute, incidents of insider threats continue to increase year over year, especially for incidents involving negligence and credential theft.
In addition, responding to, containing, and remediating insider incidents are extremely costly, averaging well over $450K per individual incident for negligence and over $800K per incident for credential theft.
We have provided several insider threat examples along with insights on how to reduce or mitigate them. Evaluating the risks tied to insider threats should also be part of every organization’s risk management process.
Linford & Company has extensive experience in assisting organizations of all sizes to manage their compliance requirements. Please contact us if you are in need of compliance or advisory services for SOC 1, SOC 2, FedRAMP, HITRUST, and HIPAA audits and assessments.
Check out these additional articles on other types of threats you should be aware of when it comes to the security of your organization:
- Considering Risk to Mitigate Cyber Security Threats to Online Business Applications
- Coronavirus Security Threats: Tips to Mitigate Cybersecurity Risks
- Mobile Security Threats: What You Need To Know For SOC 2
This article was originally published on 7/24/2019 and was updated on 3/30/2022.









