We often get questions about sharing SOC reports. The questions and answers apply to SOC 1 and SOC 2 reports alike. Besides wondering why their user organizations (clients) want a SOC report, some of the most common questions we hear from service organizations who receive a SOC report include:
- Are SOC Reports Public Documents?
- Do I Have to Share My SOC Report?
- How Do I Prove My Compliance if I Cannot Share My SOC Report?
- Can I Share My SOC Report?
- Who Can I Share a SOC Report With?
- Can I Use My SOC Report in Marketing or Post it on My Website?
- How Long is My SOC Report Valid?
- What Can I Do if There is a Gap of Time Between My Report Period & When a Client Needs the SOC Report?
- Is There a More Secure & Efficient Way For Me to Share My SOC Report With Others?
If you have one or more of these questions yourself, you will find the answers as you read on.
Are SOC Reports Public Documents?
SOC 1 reports and SOC 2 reports are not public or general use documents. They are limited in their distribution. A lot of people hear this and assume that this means that an organization cannot share its report. This assumption is incorrect. We will talk more about this later.
Do I Have to Share My SOC Report?
Service organizations often ask our firm if they have to give out their SOC report to clients or prospective clients. The short answer is no. A SOC report belongs to the service organization and they do not have to share it with anyone. While there are some legitimate reasons for not sharing a SOC report, we find that most organizations will benefit from sharing their SOC report with current or prospective clients. This is because many of them require a SOC report or a third-party certification to give them assurance about the security level of a service organization’s control environment in order to do business.
How Do I Prove My Compliance if I Cannot Share My SOC Report?
It would be difficult to prove or evidence your achievement of the specified control objectives (for a SOC 1) or Trust Services Criteria (for a SOC 2) without being able to share your SOC report. If you couldn’t share a SOC, each client or their auditors would need to come in and assess your control environment for themselves. Fortunately, you can share your SOC reports with appropriate entities. Read on for additional details on exactly who you can share the report with.
Can I Share My SOC Report?
Yes, you can share your SOC reports with those entities that are specified in the report’s limited distribution.
Who Can I Share a SOC Report With?
This is a common question. Many organizations will decline their client requests for a copy of their SOC report because they know that it is not a general use document. While it is true that there is a restriction on the report’s distribution, it is not as limited as one might think.
The auditor’s report at the beginning of a report specifies what the limitations are. For illustrative purposes, the following is an example “Restricted Use” section of a SOC 2 report:
This report, including the description of tests of controls and results thereof in Section IV, is intended solely for the information and use of ABC Corporation, user entities of ABC Corporation’s system during some or all of the period July 1, 2018 to June 30, 2019, business partners of ABC Corporation subject to risks arising from interactions with the system, practitioners providing services to such user entities and business partners, prospective user entities and business partners, and regulators who have sufficient knowledge and understanding of the following:
- The nature of the service provided by the service organization.
- How the service organization’s system interacts with user entities, business partners, subservice organizations, business partners, and other parties.†
- Internal control and its limitations.†
- Complementary user entity controls and complementary subservice organization controls and how those controls interact with the controls at the service organization to achieve the service organization’s service commitments and system requirements.†
- User entity responsibilities and how they may affect the user entity’s ability to effectively use the service organization’s services.†
- The applicable trust services criteria.†
- The risks that may threaten the achievement of the service organization’s service commitments and system requirements and how controls address those risks.
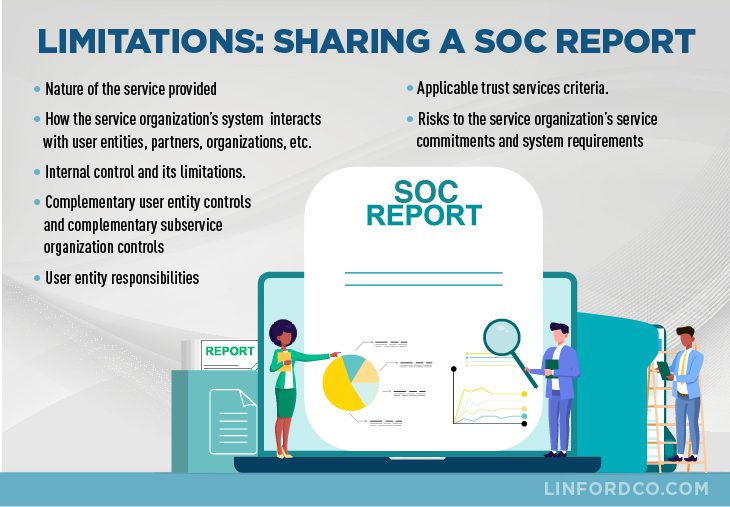
This report is not intended to be, and should not be, used by anyone other than these specified parties.
What does that all mean? Essentially, it limits the company’s ability to share the report with your:
- User Entities—clients who used the system/services for part or all of the period.
- Business Partners—those with business relationships with your organization and interact (not a user) with the system or services.
- Practitioners serving User Entities and Business Partners—This is a broad and vaguely defined group that typically creates some confusion. An organization is okay giving it to a client but will be hesitant when a client asks to share it with their auditors who have asked for a SOC report.
- Regulators—pretty self-explanatory.
Can I Use My SOC Report in Marketing or Post it on My Website?
While you are not allowed to post a SOC 1 or a SOC 2 report on a website or to use it in marketing materials, you may do so with SOC 3 report. See another one of our posts for the detailed differences between SOC 2 and SOC 3 reports and how a SOC 3 report can be used.
How Long is My SOC Report Valid?
SOC reports are retrospective or backward-looking. So, a report will always be a valid assessment for the period covered. However, what you probably want to know is, “How long will user entities accept a SOC report as evidence of your organization’s control environment?”
User entities will typically accept a SOC report for about a year after its issuance. Meaning that they will expect a new report on an annual basis. As 12 months is the typical report period, most clients will accept a report from the prior year with the assumption that another will be provided when available.
What Can I Do if There is a Gap of Time Between My Report Period & When a Client Needs the SOC Report?
The period of time covered by SOC reports vary and often does not correspond with fiscal year-end. This testing often occurs in the quarter prior to the user organization’s calendar or fiscal year-end.
For example, say a SOC report has a period ending on September 30, but the user organization has a calendar year-end of December 31. In this case, there will be a three-month gap between the attestation from the SOC examination and the user entities. You can prepare a bridge letter (a.k.a. gap letter) to bridge the “gap” between the service organization’s report date and the user organization’s year-end. See our post on “gap/bridge letters” for more details.
Is There a More Secure & Efficient Way For Me to Share My SOC Report With Others?
You or your organization should follow a formal process when sharing your SOC report. The process should address:
- Securing the SOC report;
- Making sure the person receiving the report is appropriate;
- Having recipients sign non-disclosure agreements; and
- Tracking who has received a copy of your SOC report.
Your distribution process can be simple and easily be performed manually when you have a relatively small number of requests.
Over time, as your company grows, so will the volume of requests for a copy of your SOC report whether it be from clients or potential clients. If your organization gets a SOC report, chances are you do so because it was a contractual obligation or to stop having to respond to a never-ending stream of security questionnaires. While certainly less time-consuming than completing questionnaires, it can be monotonous and disruptive to be responding to internal and external requests for your SOC report. It also increases the risk that the process of sharing your report may not be followed.
Like most processes, the more you can automate the distribution of your SOC report the less likely deviations from the process will occur. Large service providers such as Amazon Web Services (AWS), Microsoft Azure (Azure), and Google Cloud Platform (GCP) have built their own tools to automate their process of distributing SOC reports. Automating the report distribution process is not required and is less common among small to mid-sized companies due to the resources needed to develop and maintain such tools.
If you have a large number of SOC report requests, you may want to research or contact a number of entities that provide SaaS solutions that allow organizations of any size to automate their report sharing, such as Conveyor and Whistic. These types of solutions level the playing field by providing similar, if not better, solutions at a tiny fraction of the cost to develop or maintain your own tool. In fact, at the time of this post, some service providers had free versions of their tools. Doing your own research will allow you to find the solution that fits you best.
Summary
We hope this post addressing some common questions has helped you better understand the key points about sharing SOC reports. If we can help your company with a SOC 1 or SOC 2 audit, please contact us.
† source: https://www.aicpa.org
This article was originally published on 7/10/2019 and was updated on 9/8/2021.

Isaac Clarke is a partner at Linford & Co., LLP. He began his career with Ernst & Young in 2003 where he developed his audit expertise over a number of years. Isaac specializes in and has conducted numerous SOC 1 and SOC 2 examinations for a variety of companies—from startups to Fortune 100 companies. Isaac enjoys helping his clients understand and simplify their compliance activities. He is attentive to his clients’ needs and works meticulously to ensure that each examination and report meets professional standards.








