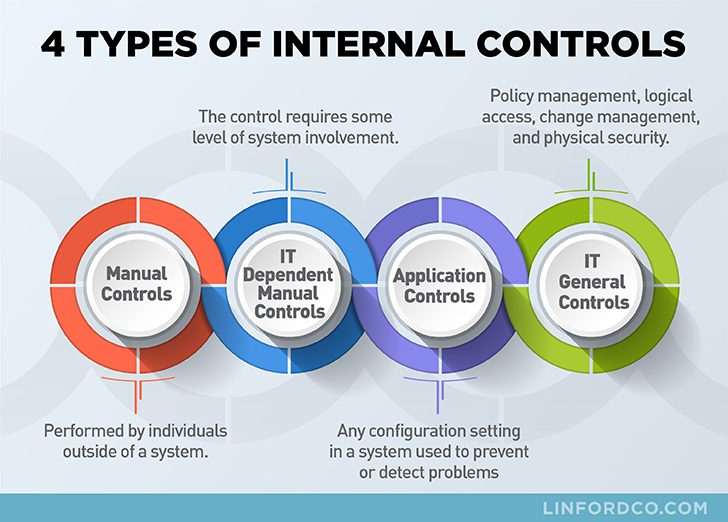
Internal controls (which include manual, IT-dependent manual, IT general, and application controls) are essential process steps that allow for one to determine or confirm whether certain requirements are being done per a certain expectation, law, or policy. Additionally, internal controls allow auditors to perform tests to gain assurance that a process is designed and operating properly.
In this post, we will discuss the definition of controls and examples of the different types of internal controls used to support business processes. Finally, we will also discuss how auditors rely on internal controls and how understanding that can help a company prepare for an upcoming SOC 1, SOC 2, HIPAA, or another type of audit.
What are Internal Controls?
According to the “Executive Summary of the Internal Control – Integrated Framework” from the Committee of Sponsoring Organizations (COSO), an “internal control is a process, effected by an entity’s board of directors, management, or other personnel, designed to provide reasonable assurance regarding the achievement of objectives relating to operations, reporting, and compliance.” The main goal of having internal controls is to set up key points in a process, which allows companies to track progress and sustainability of performance. In the next section, we will review control definitions and internal control examples.
What Are the 4 Different Types of Controls?
When performing an audit, auditors will look to see that they can gain assurance over a process by focusing on four main types of internal controls. These types of controls consist of the following:
- Manual Controls
- IT Dependent Manual Controls
- Application Controls
- IT General Controls
The four types of internal controls mentioned above are key as they are pervasive (or at least should be) in the processes that support the systems and services provided by service organizations to their user organizations (i.e. clients and customers).

What Are Internal Control Definitions & Examples?
What Are Manual Controls?
Manual controls are performed by individuals outside of a system.
What Are Some Examples of Manual Controls?
Examples of manual controls could be a supervisor review and sign-off of a document, bank reconciliation, or having an employee sign a privacy policy acknowledgment. Another example of a manual control could be the manual application (or matching) of cash received in an organization’s lockbox bank account against a client’s open accounts receivable (A/R) balance. In many organizations, these controls are done manually, hence the term manual controls.
Since the operation of these controls depends on a human, it is key that these process points have owners. When manual controls are not owned by key personnel within the organization, they often will not operate consistently. This generally poses an issue because to properly test manual controls, a sample of transactions is chosen to confirm that the control has operated for a defined period of time. If the control did not operate consistently, a deviation or exception will be noted within the audit report.

What Are IT-Dependent Manual Controls?
IT Dependent Manual Controls are similar to manual controls as they rely on a manual process from personnel but differ as a portion of the control requires some level of system involvement.
What Are Some Examples of IT-Dependent Manual Controls?
A system-generated report lists users that have not accessed (e.g., logged into a system) a particular system within the past 90 days. The internal control may require an administrator to review such reports and disable certain users whose accounts have not been accessed within the defined 90 days, as a result.
The IT-dependent portion of this control is the system-generated report. The manual portion of this control is the administrator review of the report and disabling certain users as a result.
Much like manual controls, IT-dependent manual controls should have a process owner. This will facilitate the consistent operation of these controls and avoid any exceptions being noted within an audit report.

What Are Application Controls?
There are many different forms of application controls. Virtually any configuration setting in a system that can be used to prevent or detect problems might be classified as a type of application control.
What Are Some Examples of Application Controls?
Google G-Suite and Microsoft’s Office 365 can be configured to require two-factor authentication (e.g., 2FA, MFA) in order for users to log in and access system resources and data. Enabling 2FA helps prevent unauthorized users from logging in to the system.
Another example is if the system is configured to lock out a user that enters an incorrect password after three attempts, it has an application control that detects problems possibly associated with unauthorized access attempts.
A third example could be that the system is configured to automatically download and apply security patches or updates to software (this would have likely helped prevent the Equifax hack).
Application controls which are also known as automated controls have a few benefits. One benefit is that because the control is the result of a configuration, they generally do rely on an individual to operate consistently. That being said, it is always a good idea to periodically check to confirm that the configuration has not been disabled for any reason or the configuration has not been modified.
In the event that a configuration has been modified or is no longer enabled, this can result in an exception within the report. Another benefit of having application or automated controls is that there is generally only a sample of one versus many since it is based upon a system configuration. This creates efficiency in the process and saves time during an audit.

What Are IT General Controls?
This type of control is usually the focal point of most SOC audits. IT general controls are comprised of policy management, logical access, change management, and physical security.
What Are Some Examples of IT General Controls?
User access administration controls are used so that the right people have the right access to system resources (i.e., right people & right access). These processes and the controls supporting these processes are IT general controls.
Another example could be the organization’s change management process tracks and documents that changes are authorized, tested, approved, and implemented into production. Moreover, it helps an organization gain assurance that changes happen in an environment where there is proper segregation of duties.
IT General Controls can be a combination of manual and application controls. As such, the type of sampling to test these controls varies by control type.

Preventative & Detective Controls
In addition to the types of controls named, internal controls are either preventative or detective in nature (note: sometimes corrective is added; however, it really should be considered part of detective, as in detective and corrective).
All other things being equal, preventative controls are generally superior to detective controls. The reason is this- it is usually easier and more cost-effective to correct a situation before a problem occurs than to correct a problem after detection. Those implementing internal controls into their environment will be well served by implementing a combination of preventative and detective controls with a greater focus on the former.
What Is the Purpose of Internal Controls?
The purpose of internal controls is to create touchpoints within a process that can be evidenced and reviewed and ultimately create accountability while also lowering the risk of fraud, waste, abuse, and simple mistakes.
Internal controls are generally set up by management or the Board of Directors. They set up internal controls to gain assurance that the objectives of an organization can be achieved. This can be to meet internal milestones or even external requirements such as an audit or industry standards.
Finally, internal controls allow for a company to form metrics around the efficiency and effectiveness of a process. During the review of internal controls, it can become obvious that a process is working as expected or at times the operating effectiveness of controls can prove to have failures. This allows management to determine if a different process is required to better meet company objectives.
What are Control Weaknesses?
A control weakness can fall into one of two categories. There is either a weakness in the design of a control or in its operating effectiveness. When there is a control weakness in the design of a control, that means that it was not in place, and as a result, a control failure occurred. For example, if there is a requirement for monthly patching but there is no control in place to validate that it occurs, the risk that patching does not occur and that a vulnerability can be exploited is increased. This is considered a control weakness specific to the design of a control.
The other type of control weakness is a deficiency in the operating effectiveness of a control. In this scenario, a process exists but due to a system error or personnel failure, the control does not operate as expected. Let’s go back to the server example. Let’s say that the organization has a process in which the system administrator is supposed to manually apply patches each month. However, due to turnover, patching does not occur for a number of months. The months that the server was not patched is considered a control weakness, specific to the operating effectiveness.
How Do You Strengthen Internal Controls?
The best way to strengthen internal controls is by completing a review of the current controls in place and performing a limited amount of testing to determine whether required controls operated as expected. If during the review it is determined that controls are not always operating consistently, then remediation steps should be documented and implemented. Additional testing for controls that are deficient should be re-evaluated within a few months to determine whether required implementation steps occurred.
A more formalized approach to strengthening internal controls can also be done by having a third party come in to perform a review of controls and provide input on whether a process could be updated to strengthen controls. This can be in the form of a SOC 1 or SOC 2 report, another security framework, or by having the third party complete advisory work. This can be a great option as the third party can provide their professional opinion and recommendations based on the industry standard. One thing to note is that strengthening of controls should not necessarily mean more money or a more complex process that does not align with Company requirements. When strengthening controls, the best option is generally one that streamlines the process and makes it easier to complete a control consistently, not harder.

Internal Controls & Coronavirus (COVID-19)
During these times, it may seem like working and implementing controls is either impossible or irrelevant, but in fact, in high-stress times like these internal controls are even more important. The reason for this is that stressful times can create urgency which often leads to mistakes. But with controls in place, as mentioned earlier, controls can help lower the risk that they occur or will be caught during a review. There is another major difference many companies are having to work out, which is having much of their workforce work from home. There are a number of application controls that can help a company do this while protecting client information. Below are a few application control examples that companies should consider as they continue to shore up their work from home processes.
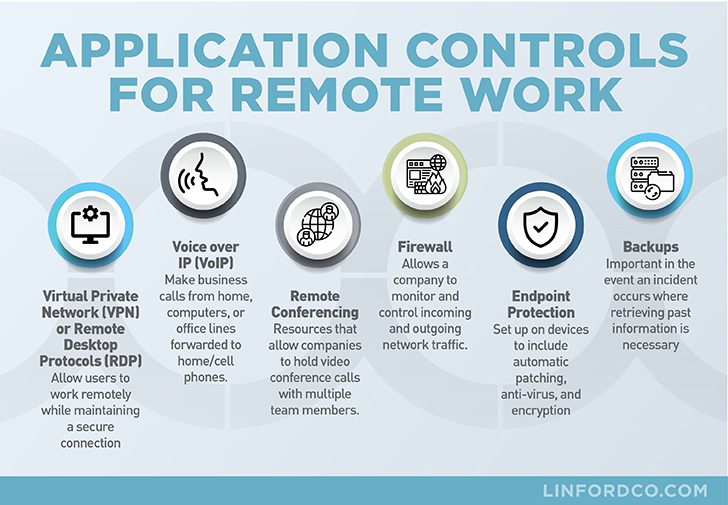
- Virtual Private Network (VPN) or Remote Desktop Protocols (RDP) – These allow users to work remotely while maintaining a secure connection to protect client information.
- Voice over IP (VoIP) – Using VoIP allows businesses to make business calls from home, from their computers, or even have office lines forwarded to home or cell phones.
- Remote Conferencing – There are a number of resources that allow companies to hold video conference calls with multiple team members. Some examples include but are not limited to Google Hangouts, Microsoft Teams, Zoom, Skype for Business, and GoToMeeting.
- Firewall – A firewall allows a company to monitor and control incoming and outgoing network traffic based on predetermined security rules.
- Endpoint Protection – Setting up endpoint protection on devices such as laptops and mobile phones to include automatic patching, anti-virus, and encryption is helpful in protecting client information being accessed or maintained from outside the network.
- Backups – Having a process in place to backup and complete restores is important in the event an incident occurs where retrieving past information is necessary.
Finally, the best course of action is to stay calm. The environment that your remote workforce is currently working in may not be perfect but that does not mean you should stress out and make decisions without proper testing and completing vendor due diligence. It’s important to keep working with the internal controls possible today and make changes as required to create a more secure environment and even better system of internal control with the main objective of protecting client information.
Summary
If the controls in the SOC audit report do not seem to fall into one of these four areas, it could be that a process is being described rather than a control.
Linford & Company service auditors work carefully with the service organizations to make sure that descriptions of the controls are accurate and support the achievement of the control objectives in a SOC 1 audit examination or Trust Services Criteria (TSC) for a SOC 2 audit examination.
It’s also important to note that these definitions and descriptions work equally well for an audit of internal control in a financial statement audit, or for internal audits.
For more information, check out these other related Linford & Company posts:
- What is an Integrated Audit? Assessing Internal Controls
- Establishing an Effective Internal Control Environment
- Understanding the Limitations of Internal Controls – Learning to Mitigate Your Risk
- Monitoring the Effectiveness of Controls at Subservice Organizations for SOC Reports
This article was originally published on 3/31/2020 and was updated on 1/25/2022.

Jaclyn Finney started her career as an auditor in 2009. She started with Linford & Co., LLP. in 2016 and is a partner with the firm. She is a CISA with a special focus on SOC, HITRUST, FedRAMP and royalty examinations. Jaclyn works with her clients to provide a process that meets the needs of each customer and generates a tailored report that is useful to the client and the users of the report.




