For organizations beginning their HITRUST® adoption and certification journey, the path forward often looks complex. The single most critical first step? A comprehensive readiness assessment. In this guide, we will cut through the noise and cover:
- Assessment Types: The different forms of readiness assessments, and which one fits your specific needs.
- Common Pitfalls: The specific challenges organizations face during this phase, and how to avoid them.
- Success Factors: The key elements that turn a standard assessment into a strategic win.
- The Roadmap: The crucial steps bridging the gap between your readiness assessment and final certification.
While this article is focused on HITRUST adoption, the basic readiness assessment concepts presented can be applied to nearly any framework or regulatory requirements, including SOC 2, PCI, FedRAMP, NIST, CMMC, HIPAA, GDPR, and others.
HITRUST has recognized the need for certifiable and reliable information security assessments and, with the collaboration of industry leaders, developed a standardized approach to assessing an organization’s risk posture. If the organization meets this standard by completing one or more types of validated assessments, a certification can be issued and presented to business partners to convey assurance to other organizations in relation to the protections in place for sensitive information.
To meet this standard, organizations must go through a robust process that ends with a validated assessment performed by an approved third-party assessor, the review and validation of the assessment by HITRUST, and, if successful, certification under one of the following:
- Essentials (e1) Validated Assessment + Certification
- Leading Practices (i1) Validated Assessment + Certification
- Expanded Practices (r2) Validated Assessment + Certification
Choosing Your HITRUST Assessment Strategy
When it comes to gauging your readiness, there are generally two approaches. Choosing the right one depends on your internal expertise and risk appetite.
- Self-Assessment (The DIY Approach): This is performed entirely with internal resources. While cost-effective upfront, it relies 100% on your team’s interpretation of the HITRUST CSF (Common Security Framework).
- Pros: Low immediate cost, internal control.
- Cons: High risk of misinterpreting controls, “optimism bias” in scoring, and lack of validation.
- Third-Party Facilitated Assessment (The Expert Approach): In this model, you engage a subject-matter expert (SME) to guide the process. This isn’t just about checking boxes; it’s about getting professional feedback on how you are meeting requirements before the official audit begins.
Our Recommendation: We strongly advise engaging an Authorized External Assessor or a partner with deep experience in the ecosystem. HITRUST is nuanced; an external partner makes certain you aren’t just guessing at the answers. They bring the objectivity and rigor required to pass the actual validation later.
Once the overall strategy has been defined, it is important to pause and consider the risks associated with executing the readiness activities. One of the most vital steps is to properly plan to engage the correct resources and plan for a sufficient level of effort to provide meaningful insights into the readiness process.
Garbage In, Garbage Out: Why Assessments Fail
A readiness assessment is only as valuable as the effort and honesty you put into it. If you rush the input, you will get a flawed roadmap that leads to failure during the actual validation.

The Organizational Friction
The first major hurdle lies within your own internal structure. It is remarkably common to assume specific security roles are covered, only to discover during the assessment that ownership is undefined. This is why active stakeholder involvement is critical; without a visible “tone at the top,” the assessment is often treated as a low-priority distraction. Furthermore, resource contention is a constant reality. Your team is likely already stretched thin by conflicting priorities and remote work silos, meaning clear guidance from leadership is the only way to make certain the assessment gets the attention it requires.
The Technical Blind Spots
Visibility creates the second friction point. You cannot assess what you cannot access, and delays often stem from simply hunting down the specific administrator with rights to MDM consoles or AV portals. Even more critical is the state of your asset inventory. If your inventory is incomplete, your scope is wrong; if your scope is wrong, your certification is invalid. This is exacerbated by “cloud sprawl”—unmanaged cloud services that pop up unexpectedly. Finding these governance gaps during a readiness assessment is a headache, but finding them during your final audit is a disaster.
The Assessment Mechanics
Finally, you must master the mechanics of the assessment itself. A frequent pitfall is the “optimism bias” in scoring, where internal teams inflate their maturity scores due to a lack of understanding of HITRUST’s rigorous standards. You also need to understand the specific evidence required—knowing whether a control requires a simple interview (inquiry) or a system configuration review (inspection) is vital for preparation. All of this relies on your Subject Matter Experts (SMEs). Unfortunately, the System Architects and Engineers with the answers are usually the busiest people in the company, making the “SME bottleneck” a consistent threat to your timeline.
In the following sections, we will review a number of the most common pitfalls that may occur in organizations that are operating without a complete understanding of the HITRUST requirements, scoring methodologies, the assessment process, and the minimum expectations for certification.

Pitfall 1 – Improper Scoping Factors or Assessment Selection
The HITRUST CSF (Cyber Security Framework) is the embodiment of this standard. It includes a pool of requirements that have been refined over decades from over 40 authoritative sources, including NIST, ISO, PCI, HITRUST CSF (Common Security Framework): A Beginner’s Guide, GDPR, CCPA, and more. Just how many HITRUST controls are there? This pool has just under 2,000 requirements, but don’t panic — only a small percentage of these will remain after the scoping step below. This framework is accessed through a web interface called MyCSF.
What Is MyCSF®?
Think of MyCSF as an empty desk that is waiting to have all the documents for a project put into the drawers while providing mechanisms to evaluate and grade the documents.
What Are Scoping Factors?
In simple terms, scoping factors are the criteria used to figure out what needs to be included in a security assessment or audit. They help determine the boundaries and extent of the systems or environments that require evaluation to validate security and compliance. In HITRUST vernacular, scoping factors can be considered the “demographics” of the implemented system which is to be assessed.
It is important to note that the scoping factors selection process discussed next relates only to the r2 Validated Assessment. It does not apply to the e1 or i1 Validated Assessments since the e1 and i1 are non-tailored assessments.
How are Scoping Factors Determined?
As part of the r2 Validated Assessment, the scoping factors selection process within MyCSF identifies which requirements are needed for certification that pertain to your organization. MyCSF provides a series of questions that, from the responses, will develop a pool of requirements. These questions include things like:
- How big is the organization?
- What type of organization?
- Do you need to include state regulatory requirements?
Do you use hardware tokens for multifactor authentication?
- Where is covered data stored, processed, or transmitted?
While these questions seem simple enough, there are significant implications for your responses. Some questions are very straightforward. For example, your type of organization is probably not going to change based on how you answer other questions. If you are an IT service provider, you are not likely to need to change that to a health information exchange. But other questions might change based on where in the organization you apply them. If you use hardware tokens for authentication in the corporate office only and the office is not in scope for the assessment, answering yes to this question will add several requirements that really don’t pertain to the in-scope environment.
There are a number of questions regarding accessing the environment from the internet, public networks, or kiosks. Again, these responses should include careful consideration of what systems and networks are in scope. It goes without saying that truthful answers must be given to all questions. But truthful for many of these could be a yes or a no, and if you are not sure, then consult an experienced external assessor.
As mentioned above, the scoping factors only apply to the r2 Validated Assessment. However, the same pitfall can occur when an organization selects the wrong assessment based on its needs and the needs of those who will ultimately request and review the HITRUST certification obtained by the organization. Again, speaking to an experienced external assessor can help guide organizations on their path to selecting the appropriate assessment within the HITRUST assessment portfolio.

Pitfall 2 – Improper Scope Definition
Pitfall 2 is related to pitfall 1. Once you have answered all the scoping factors questions correctly, you will generate the set of requirements that really define the assessment. Pitfall 2 occurs when you apply a requirement to a system or network that should be out of scope, or don’t apply it when you should.
What Is the Scope of the HITRUST Readiness Assessment?
The scope of the assessment differs from the process of selecting scoping factors. Scoping factors determine what requirements are applicable for a given r2 Validated Assessment, but the scope of the assessment has to do with the people, processes, technologies, and other elements that will be considered “in-scope” for the assessment.
When determining the scope of an assessment, several important criteria should be considered. These criteria help identify the specific areas, processes, and controls that need to be assessed to achieve the assessment objectives. While the importance of specific criteria may vary depending on the nature of the audit, it is important to review and refine the scope of the assessment as needed until both the assessed entity (the entity pursuing certification) and the external assessor organization reach a shared understanding of the intended scope.
The scope is like a roadmap that tells the external assessor what specific areas or aspects they should pay attention to during the assessment. It helps keep the assessment focused and verifies that the right things are being examined to make sure everything is in order and meets the necessary HITRUST requirements. Just like you wouldn’t want to be operating a GPS with outdated maps on it, a complete and accurate definition of scope in an assessment is critical to success. Errors, omissions, and other issues associated with scope are one of the biggest pitfalls organizations face during a readiness assessment, because either too much or too little is being considered.
How Do You Verify the Scope of an Assessment?
One way to answer the question of what systems or networks are in scope is through a review of an accurate network/flow diagram. Find the heart of the environment – the place where the service that you want to certify is hosted. Look for where the data is stored, processed, or transmitted. Are there dedicated security boundaries between the in-scope systems and the systems under question? If no firewall or other security mechanism is restricting or controlling data flow or access, then the system under question is likely to be in scope.
For example, if the service you wish to certify is hosted in your data center and you have an employee-only wireless network in the office, is the wireless network in scope? The answer depends on several questions. Can a wireless user directly access covered data from their laptop? Are there security controls in place, like VDI or terminal server interfaces that must be used to access data? Does the wireless user have to connect through a VPN before accessing covered data? All of these will determine if the wireless network should be considered during the assessment.
This guidance applies equally to all HITRUST assessments. It is very important to work with an external assessor organization (preferably the one that will ultimately perform the validated assessment) since a shared understanding of the scope and applicability of requirements is vital to the success of the certification effort.

Pitfall 3 – Evaluation and Scoring
I am going to state right up front that HITRUST scoring involves high-level mathematics and maybe some good ole Kentucky windage. For the r2 Validated Assessment, each HITRUST requirement is scored from five different perspectives –
- Policy
- Procedure
- Implementation
- Measured
- Managed
Each of these is weighted, and the aggregate weight equals 100%. During an assessment, a percentage is assigned to each from a list of 0%, 25%, 50%, 75%, or 100%, and a special N/A (not applicable). There are specific requirements for each of these levels.
One of the approaches I have used in helping organizations prepare to perform their own, unassisted readiness assessments is to go through several typical requirements and evaluate and score evidence from their environment. It is very easy for the first-timer to over-rate their position and underestimate the requirement. To remove lots of confusion and increase alignment with what HITRUST expects, I refer to a table published by HITRUST called the scoring rubric.
The scoring rubric is a grid that includes all five aspects to be considered versus the six possible scores. In each corresponding cell is a definition that must be applied for that specific score. Any deviation from this approach during the readiness assessment will increase the deviation from the validated assessment. To support consistency during readiness and validated assessments, assessed entities should be just as familiar with the rubric as assessors. If assessed entities are interested in training internal resources, HITRUST offers a Certified CSF Practitioner Course.
How Does Scoring Work for the e1 and i1 Assessments?
The difference between the e1, i1, and r2 when it comes to scoring is rather simple. The r2 assessment includes all five maturity levels described above. The e1 and i1, on the other hand, include only the “implementation” maturity criteria for the assessment. This does not mean that things like policies and procedures do not matter in the i1 assessment, but they are not scored separately.

Pitfall 4 – Misunderstanding HITRUST Requirements
The HITRUST CSF includes specific terms, concepts, and expectations that the first-time user may not appreciate. Terms like measured, managed, metric, independent, and operational all have very specific meanings that might change in different contexts. It is important to apply the expected definition to these terms as the third-party assessor will.
For example, one aspect of a requirement is how well the organization “measures” the effectiveness of the control. An organization might do this through a review of a report. It is important to know who generated the report, how often the report is reviewed, and what it includes. If the report is generated by the team that manages the control, it is considered operational and is limited to a maximum score. If the report is run every week and a number can be identified to track effectiveness from cycle to cycle, it can be considered a “metric.” Metrics have a higher possible score than a measurement.
Navigating this specialized vocabulary while simultaneously managing scope, evidence, and scoring nuances represents a significant undertaking for any organization approaching HITRUST for the first time. The sections that follow in ‘Turning Challenges into Certification’ are designed to transform these common stumbling blocks into a clear, actionable path forward.

Turning Challenges into Certification: The Guide to Success
While the hurdles to HITRUST readiness are significant, the formula for success is actually quite consistent. It starts with the single most critical factor in any engagement: defining the scope. You must ruthlessly define which people, processes, and technologies are in the “boundary” and which are out. A fuzzy scope leads to “scope creep,” wasted budget, and failed validations. Therefore, we adhere to a strict rule: until the scope is explicitly defined and agreed upon, the assessment does not begin.
Once the scope is set, you must move beyond simple Q&A. Executing a readiness assessment based solely on inquiry—taking people’s word for it—is a recipe for a low-quality result. Instead, you need an approach based on inspection and observation. It is common for a manager to say, “All new hires complete security training,” but a successful assessment demands that you pull the logs to prove it. By validating assumptions with hard evidence during the readiness phase, you eliminate the panic of scrambling for proof during the actual audit.
Finally, success depends on mastering the HITRUST Scoring Rubric. Everyone involved in the assessment must understand that HITRUST scoring is nuanced; it is not a simple pass/fail. You must adopt a philosophy of disciplined conservatism. It is far better to score yourself harshly now and identify gaps than to be overly optimistic and fail the validation later. The goal is to align your internal perspective with the harsh reality of an external assessor’s standards, ensuring that when you finally submit your scores, they are defensible and accurate.
Decoding the Jargon: Research & Evaluative Elements
To truly succeed, you must go deeper than the surface-level requirement statements. You need to master the Evaluative Elements—the specific, granular criteria that auditors use to grade your performance.
While the MyCSF® portal provides the raw data and illustrative procedures, navigating it can often feel like reading a foreign language. This is where the value of a skilled assessor becomes undeniable. We don’t just read the requirement statements to you; we translate them. We bridge the gap between abstract compliance language and your specific technology stack, ensuring you understand not just what the control says, but how it applies to your unique environment.
Don’t Reinvent the Wheel: Inheritance & Reliance
Modern organizations rarely operate in a vacuum; you rely on internal shared services and external partners like Cloud Service Providers (CSPs) to function. The good news is that HITRUST allows you to claim credit for the security work they have already done. There are generally three ways to demonstrate this, split into two categories: Inheritance and Reliance.
The Gold Standard: Internal & External Inheritance
Inheritance is essentially “downloading” a passing score into your assessment. Internal Inheritance allows you to take scores from one of your own HITRUST-certified internal divisions and apply them to another. External Inheritance is even more powerful; it allows you to pull scores directly from a vendor’s certification (like AWS or Azure) through HITRUST’s Shared Responsibility and Inheritance Program. This is the cleanest, most efficient way to demonstrate compliance because the scores are pre-validated and formatted specifically for the HITRUST framework.
The Backup Plan: Reliance
When inheritance isn’t an option, you may turn to Reliance. This involves taking a third-party audit report (like a SOC 2 Type II) and trying to map it to your HITRUST requirements. Be warned: this is often like trying to fit a square peg into a round hole. The scope of a third-party audit rarely matches the granular precision of a HITRUST assessment, and the level of testing detail may not satisfy your assessor. While it is a valid path, it requires significant effort to bridge the gaps in scope and evidence.
Strategy Over Checkboxes: The Remediation Roadmap
You cannot fix everything overnight. A successful readiness assessment doesn’t just hand you a depressing list of flaws; it gives you a strategic battle plan. Instead of trying to patch every single vulnerability at once (“boiling the ocean”), you need a risk-based approach. You must identify and prioritize the gaps that pose the biggest threat to your actual security posture, rather than just chasing compliance for compliance’s sake.
The Math of Certification: At the end of the day, getting HITRUST certified is a math problem. Your final status is determined by averaging scores across specific domains. You do not necessarily need a perfect 100% on every single control to pass; you need a calculated average that meets the certification threshold. While the specific calculus of HITRUST scoring is complex (and covered in our other technical guides), the takeaway here is simple: Smart remediation doesn’t mean fixing everything; it means fixing the right things to make the math work.
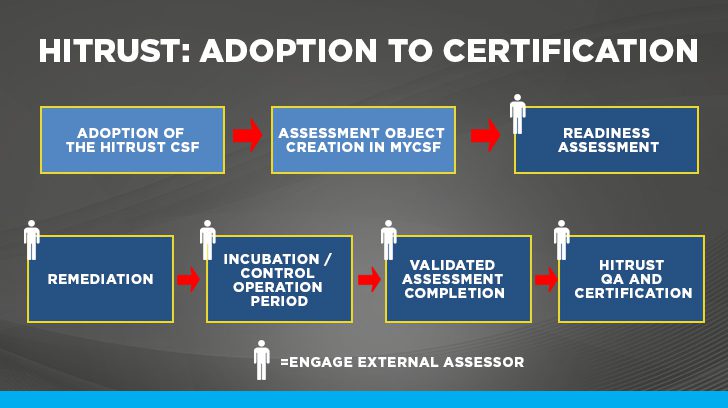
The Roadmap: From Readiness to the Finish Line
One of the most common questions we receive is, “How long will this take?” While every organization is unique, the typical timeline from the start of a readiness assessment to the completion of a validated assessment ranges from four months to a year. This is a marathon, not a sprint, and the graphic below outlines the standard milestones you will hit along the way.
However, it is crucial to view this timeline through the right lens. We operate on the philosophy that security creates compliance as a byproduct. If you focus solely on “getting the badge,” the process will feel like a burden. But if you focus on HITRUST adoption as a mechanism to mature your security posture, the certification becomes the natural result of doing the right thing. This mindset creates positive momentum, turning a check-the-box exercise into a strategic initiative that protects your data and builds trust with your clients.
Frequently Asked HITRUST Questions
The following are some of the most common questions we are asked by clients when it comes to HITRUST readiness and the certification process.
My Organization Needs to Get HITRUST Certified – What Should We Do First?
The first step isn’t just research; it is conversation. While it is helpful to review the available certifications on the HITRUST website, your most effective move is to reach out to an Authorized External Assessor immediately. We recommend setting up a scoping call right away. We cannot give you an accurate timeline or price until we understand the high-level details of your environment, so let’s start that dialogue before you get lost in the weeds of technical documentation.
Which HITRUST Certification Is Right for Our Organization?
The “right” certification usually depends on who is asking for it. Is this demand driven by a specific external business partner (like a large hospital system or payer), or is it an internal initiative to mature your security program? To give you a concrete recommendation, we need to understand exactly who you serve and what sensitive data you hold. That candid conversation is the foundation of the scoping process, ensuring you don’t over-engineer a solution for a simple problem, or under-scope a complex one.
Can Our External Assessor Help Us with the Readiness Assessment & the Validated Assessment?
Yes, and this is often the most efficient path. However, we protect the integrity of your certification by managing conflicts of interest with strict conservatism. We maintain a “separation of church and state”: the specific personnel who guide your readiness assessment will not be the same people grading your final validated assessment. Furthermore, we do not provide managed IT services. This makes certain that our auditors are always objective, grading your controls rather than checking their own homework. With that foundation in place, the next step is simply taking it, and you don’t have to take it alone.
Ready to Start Your HITRUST Readiness Process? Let’s Talk
We hope this guide has demystified the readiness assessment process. Whether you are tackling HITRUST certification, a SOC 2 audit, or any other regulatory standard, the principles remain the same: define your scope, validate your evidence, and execute with strategy.
If your organization is just beginning this journey—or if you are looking for a partner to turn a chaotic process into a streamlined one—we are here to help. The team of experienced auditors at Linford & Company specializes in making the complex simple. Reach out to us today, and let’s discuss how we can make your next assessment less painful and more valuable.

Richard Rieben is a Partner and HITRUST practice lead at Linford & Co., where he leads audits and assessments covering various frameworks including HITRUST, SOC, CMMC, and NIST. With over 20 years of experience in IT and cybersecurity and various certifications including PMP, CISSP, CCSFP, GSNA, and CASP+, Richard is skilled in helping growing organizations achieve their information security and compliance goals. He holds a Bachelor of Science in Business Management and an MBA from Western Governors University.