What is the Difference Between the NIST Cybersecurity Framework & NIST 800-53?
I used to perform NIST 800-53 audits and eventually learned to appreciate the structure and rigor that the 800-53 framework brought to federal information systems and entities. However, it is not widely adopted by commercial entities, particularly those smaller companies or entities just starting their IT compliance journey. Enter NIST CSF.
According to NIST, the Cybersecurity Framework was “Created through collaboration between industry and government” with the goal of defining “standards, guidelines, and practices to promote the protection of critical infrastructure. The prioritized, flexible, repeatable, and cost-effective approach of the Framework helps owners and operators of critical infrastructure to manage cybersecurity-related risk.”
NIST CSF v1.1
Image Source: https://www.nist.gov/cyberframework
A Closer Look at NIST Cybersecurity Framework Version 1.1
When choosing a cybersecurity framework, it’s important to consider your organization’s strategic objectives, risk profile, and applicable laws and regulations. While the leading industry information security frameworks share common objectives and controls, the requirements and level of effort to implement each varies. For example, NIST 800-53 is one of the most robust and prescriptive frameworks, with 18 control families and over 900 controls. The NIST CSF is a subset of NIST 800-53, sharing certain requirements and criteria, while omitting many of the controls more relevant to federal agencies.
The NIST CSF is scalable and aligns with industry best practices for cybersecurity, making it an attractive option for commercial entities, especially those that are just starting to implement cybersecurity policies and controls. Key framework attributes include:
- Common and accessible language
- Adaptable to many technologies, lifecycle phases, sectors, and uses
- Risk-based
- Based on international standards
- Living document
- Guided by many perspectives – private sector, academia, public sector
What are the Main Components of the NIST Cybersecurity Framework? How Many Controls are in the NIST CSF?
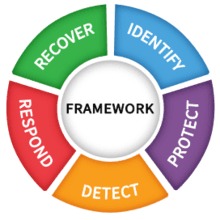
Officially released in 2014 with an updated version in 2018, the Framework Core is organized into 5 functions and 23 “categories”. Each category contains a number of subcategories, totaling 108 across the 5 functions and 23 categories. The subcategories are essentially the stated control activities.
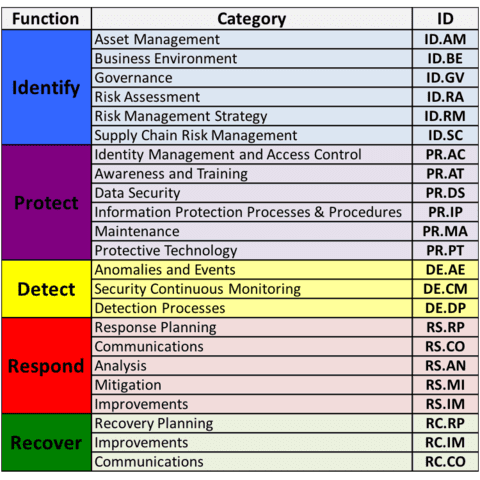
NIST CSF v1.1 Functions & Categories
Image Source: https://www.nist.gov/cyberframework/online-learning/components-framework
While streamlined, the NIST CSF is prescriptive and clearly stated in “plain English” such that organizations are able to interpret the standards and requirements with relative ease. You’ve likely read various frameworks and were left wondering if a translator was available. On the contrary, the NIST CSF is written in a more concise, user-friendly manner.
For example, the below table highlights the CSF’s identity and access management principles, with clear subcategories suggesting how to implement controls that would achieve the stated principle/requirement:
| NIST CSF Components | ||
|
FUNCTION
|
CATEGORY
|
SUBCATEGORY
|
| Protect (PR) | Identity Management, Authentication and Access Control (PR.AC): Access to physical and logical assets and associated facilities is limited to authorized users, processes, and devices, and is managed consistent with the assessed risk of unauthorized access to authorized activities and transactions. | |
| PR.AC-1: Identities and credentials are issued, managed, verified, revoked, and audited for authorized devices, users and processes | ||
| PR.AC-2: Physical access to assets is managed and protected | ||
| PR.AC-3: Remote access is managed | ||
| PR.AC-4: Access permissions and authorizations are managed, incorporating the principles of least privilege and separation of duties | ||
| PR.AC-5: Network integrity is protected (e.g., network segregation, network segmentation) | ||
| PR.AC-6: Identities are proofed and bound to credentials and asserted in interactions | ||
| PR.AC-7: Users, devices, and other assets are authenticated (e.g., single-factor, multi-factor) commensurate with the risk of the transaction (e.g., individuals’ security and privacy risks and other organizational risks) | ||
When establishing the CSF, NIST attempted to strike a balance of addressing the full lifecycle of cybersecurity without being overly detailed or too prescriptive. As a result, the subcategories were intentionally written as outcome-driven statements to foster risk-based decision-making, enabling organizations to implement policy and control solutions tailored to their environment.

Mapping the SOC 2 Criteria to the NIST Cybersecurity Framework
Part of NIST’s vision with the CSF was to design a framework that logically aligned and mapped to other leading industry frameworks. Within the NIST CSF, you will find Informative References that tie each of the CSF subcategories to their industry counterparts, including the following:
- Center for Information Security (CIS) Framework
- COBIT 5
- ISA/IEC 62443 Cybersecurity Certificate Programs
- ISO/IEC 27001:2022 Information Security Management
- NIST SP 800-53 rev. 4.
Beyond that, you can readily find NIST CSF mappings to SOC 2 (TSC mappings), PCI, and HIPAA on the internet.
Now that we’re neck-deep in compliance acronym soup, you are likely asking yourself again why you should care about another framework. I like to think of the NIST CSF as a great foundation for developing your policy statements and standards that form your internal controls, which can then be mapped to the relevant Trust Services Criteria to support your SOC 2 compliance journey.
Take our earlier NIST Subcategory example, and note how it maps to the Trust Services Criteria (note, use the mapping spreadsheet referenced above to easily search by NIST Subcategory reference or SOC 2 Criteria reference):
| SOC 2 mapping to NIST CSF (example) | ||
|
CSF FUNCTION
|
CSF CATEGORY & SUBCATEGORY
|
TRUST SERVICES CRITERIA & POINTS OF FOCUS
|
| Protect (PR) | Identity Management, Authentication and Access Control (PR.AC): Access to physical and logical assets and associated facilities is limited to authorized users, processes, and devices, and is managed consistent with the assessed risk of unauthorized access to authorized activities and transactions.
PR.AC-1: Identities and credentials are issued, managed, verified, revoked, and audited for authorized devices, users and processes |
CC6.1: The entity implements logical access security software, infrastructure, and architectures over protected information assets to protect them from security events to meet the entity’s objectives.
|
CC6.2: Prior to issuing system credentials and granting system access, the entity registers and authorizes new internal and external users whose access is administered by the entity. For those users whose access is administered by the entity, user system credentials are removed when user access is no longer authorized.
|
||
As you can see from this example, the NIST CSF subcategory statement is written in a concise, but comprehensive, manner that could be used to form a policy statement or control activity. That singular control activity could then be mapped to multiple SOC 2 Criteria, not to mention other leading industry frameworks.

NIST Cybersecurity Framework vs SOC 2 Audits
Now you may be asking, “If the NIST CSF is so efficient, why do I need a SOC 2? And how do I become NIST certified?” Valid questions. You likely still need a SOC 2 Report because it’s the leading industry standard used by service organizations to convey assurance over system and organization controls. This is done by an independent auditor who issues a report attesting to the service organization’s compliance with the Trust Services Criteria.
On the contrary, there is no such attestation available for the NIST CSF. According to NIST, “NIST has no plans to develop a conformity assessment program. NIST encourages the private sector to determine its conformity needs, and then develop appropriate conformity assessment programs.” Additionally, “The Framework was created with the current regulatory environment in mind, and does not replace or augment any existing laws or regulations. The Framework leverages industry best practices and methods for cybersecurity risk management, which are often used in regulation.”
In other words, the NIST CSF is intended to be a useful tool for organizations looking to design and implement cybersecurity policies and controls that will satisfy multiple regulatory and compliance requirements. If you are a service organization, chances are you still need that SOC 2 report, but the NIST CSF can help you interpret the foreign language that is the Trust Services Criteria and be the “how-to” you’ve been looking for.

What is a SOC 2+ and How Does it Relate to the NIST CSF?
Still not convinced there’s a way to bring all these acronyms together? In fact, the governing body for SOC 2 audits, the American Institute of Certified Public Accountants (AICPA), has developed an option that allows a service organization to obtain a “SOC 2+”. The SOC 2+ is a SOC 2 examination that “Addresses Additional Subject Matters and Additional Criteria”. In this case, the service auditor identifies the additional subject matter being reported on or the additional criteria (e.g., the NIST CSF Subcategories) being used to evaluate the subject matter and report on the additional subject matter.
Other examples of this reporting option are those reports that include information on a service organization’s ability to meet the requirements of HITRUST, HIPAA, or the Cloud Security Alliance’s Cloud Control Matrix. The auditor will include additional tests of controls that achieve the additional criteria, and may include a mapping between the criteria in order to demonstrate the service organization’s alignment between the compliance frameworks. This may or may not be a value-add to your organization, but it’s a relatively low level of effort that may be worth it if you operate in an industry that expects compliance with other frameworks beyond SOC 2. As with all audit-related decisions, it’s best to discuss the options and potential benefits of each with your service auditor.
In Conclusion…
Still drowning in acronym soup? Curious how your organization may benefit from the NIST CSF, a SOC 2 Report, or even a SOC 2+ Report? At Linford & Company, we live and breathe the audit and compliance world and are happy to discuss how to best align your compliance activities with your organization’s strategic objectives, risk profile, and applicable laws and regulations. You are not in this alone – contact us today!

Maggie has over 15 years of experience in Risk Management and IT Compliance. She spent nearly 10 years in KPMG’s IT Advisory and Attestation practice before joining a financial technology company as the Risk and Compliance Director. She has overseen numerous SOC 1 / SOC 2 audits and other IT Compliance audits and has vast experience implementing risk management and IT compliance solutions. She is Certified in Risk and Information Systems Control (CRISC) and obtained a Bachelor of Science in Business Administration, Finance, from the University of Colorado at Boulder.