Founded in 2007, HITRUST® issues certifications to businesses and organizations that are independently assessed for compliance with its Common Security Framework (CSF®).
This guide will walk you through the HITRUST certification process, explain all available assessment types (e1, i1, r2), introduce newer offerings tailored to AI systems, and provide guidance on maintaining certification over time. Whether you’re pursuing HITRUST for the first time or seeking to deepen your understanding, this comprehensive article aims to clarify the process, reduce confusion, and position your organization for long-term success.
What is HITRUST Certification?
HITRUST certification is a formal recognition that an organization has successfully demonstrated compliance with the HITRUST Common Security Framework (CSF®) through an independent, third-party validated assessment. This certification provides assurance to clients, partners, and stakeholders that the organization maintains robust information security controls and practices.
Assurance of a secure operating environment is a challenge that has rapidly spread across industries. Recent breaches have shown how supply chain attacks can have significant downstream impacts. The interesting thing to note is that most recent high-profile attacks could have been prevented through the application of sound cyber hygiene practices, such as those required of organizations undergoing HITRUST certification. Several examples include the usage of strong, advanced authentication mechanisms, the ability to identify and prevent the usage of weak credentials, and more.
Organizations operating in regulated industries such as healthcare, finance, and cloud services are increasingly turning to the HITRUST CSF® framework to demonstrate robust security and compliance.
Understanding the HITRUST CSF Framework
An organization can obtain HITRUST certification when all the required controls are fully implemented within the scoped environment. The HITRUST CSF is designed for use by a variety of organizations that may create, access, store, or share sensitive data. The CSF incorporates commonly accepted standards such as ISO, NIST, PCI, HIPAA, and COBIT within its baseline security controls. It offers a scalable, prescriptive approach to information risk management. Designed to be flexible across industries, the CSF allows organizations to demonstrate compliance with a wide variety of regulatory requirements using a single, comprehensive framework. MyCSF®, the HITRUST cloud-based SaaS platform, is central to administering assessments, uploading evidence, and tracking compliance milestones.

Types of HITRUST Assessments
HITRUST offers both self-guided and third-party validated assessments. These assessments are designed to meet organizations where they are in terms of maturity and risk. The main types of assessments include:
- Readiness Assessment: Helps identify gaps and prepare for formal evaluation.
- Self-Assessment: Internal teams complete assessments using MyCSF without third-party validation; suitable for internal readiness checks.
- Validated Assessments: Provide formal HITRUST certification and involve third-party assessors to verify evidence and scoring.
HITRUST provides a structured suite of three key cybersecurity assessments and certifications—e1, i1, and r2—tailored to an organization’s size, risk profile, and security needs. Since all three assessments are built on the HITRUST Framework (HITRUST CSF®), previous assessment efforts can be leveraged when pursuing more advanced certifications. Additionally, organizations can inherit existing controls from certified cloud service providers to streamline their compliance efforts.
HITRUST e1 – 1-year Validated Assessment
This is the entry-level validated assessment that focuses on foundational cyber hygiene. It is ideal for startups, small healthcare providers, or organizations with minimal regulatory exposure. The e1 includes around 44 core control requirements and offers a manageable entry into the HITRUST ecosystem. Certification is valid for one year.
HITRUST i1 – 1-year Validated Assessment
The i1 assessment goes beyond basic hygiene and covers a more comprehensive set of controls (~182 as of CSF v11). It’s intended for organizations with moderate risk exposure that require a higher level of assurance. This assessment does not include risk scoping but includes a rapid recertification option to streamline annual renewal.
HITRUST r2 – 2-year Validated Assessment
The most comprehensive HITRUST assessment, r2 is tailored to organizations with complex infrastructures and significant regulatory obligations. It supports risk-based scoping and uses the PRISMA maturity model, which evaluates controls across five dimensions. r2 certification is valid for two years, with an interim assessment required at the end of year one.
HITRUST Assessment & Certification in the AI Ecosystem
As artificial intelligence plays an increasing role in data processing and decision-making, HITRUST has introduced AI-specific assessment offerings to manage the unique risks associated with AI deployments:
AI Risk Management Assessment
The HITRUST AI Risk Management Assessment delivers in-depth insights based on 51 practical and relevant AI risk management controls. Aligned with ISO 23894 and the NIST AI RMF, this assessment offers a streamlined control framework, enabling organizations to evaluate and report their performance in accordance with ISO and NIST standards.
AI Security Assessment & Certification
The HITRUST AI Security Assessment equips AI platforms and service providers with practical, prescriptive security controls and methodologies to securely adopt AI technologies. It supports shared responsibility inheritance and, when combined with an e1, i1, or r2 certification, helps organizations efficiently meet multiple compliance requirements within a unified framework.
Separating the assessments and certifications in detail is a topic that will likely warrant its own discussion in the future, but for now, there are three key differences worth focusing on:
- The e1 and i1 assessments are based on a static set of controls, unlike the r2, which is based on scoping factors. The r2 certification will still vary in size from one organization to another.
- The e1 and i1 are based simply on the implementation of controls, with minimal dependence on document policies, unlike r2 assessments, which consider five levels of maturity: policy, procedure, implemented, measured, and managed.
- The e1 and i1 can lead to ONE year of certification, whereas the r2 can lead to two years of certification based on the completion of an interim assessment at the one-year mark. There is a rapid recertification process in place for the i1, which will focus on compliance with a subset of i1 requirements to be re-certified. There is no rapid recertification option for the e1 certification.
- The AI Security assessment and certification may be paired with an e1, i1, or r2 to result in a formal certification of AI Security.

How Do I Get HITRUST Certified?
If you are reading this, you may well be considering obtaining a HITRUST Certification. Some people may call it CSF certification, but the correct term is HITRUST certification. This post will walk you through the overall HITRUST certification process. You will learn the major steps needed to prepare, be assessed, and obtain the certification. We will also highlight some of the pitfalls to avoid along the way.
If you are not quite ready to dive into the HITRUST assessment processes but would like to learn more about HITRUST, I recommend that you take a look at one of our earlier blogs that walks you through the basics of HITRUST compliance.
How to Prepare for a HITRUST Assessment
While you will need to receive and submit a validated assessment to HITRUST for certification, it is recommended that your organization start with a self-assessment or readiness assessment. A HITRUST self-assessment is performed internally by your own personnel against CSF, while a readiness assessment is typically performed by an independent third party. Either of these assessments will help familiarize your business with CSF requirements and identify any control gaps that should be addressed before going forward with a validated assessment. Read here to learn about potential HITRUST self-assessment pitfalls to avoid.
We recommend organizations have a readiness assessment performed by the HITRUST External Assessor Organization, which will ultimately be performing their validated assessment. This provides you with the assessor’s perspective of the gaps that need to be addressed and allows you an opportunity to discuss any differing opinions regarding those gaps and how best to address them. Either way, be sure to be thorough. This is the time to catch any shortcomings. If you perform a self-assessment independently, the last step of preparation is to engage a HITRUST External Assessor Organization to perform your validated assessment.
Do You Need the HITRUST MyCSF Tool?
Another important item to decide is how much you plan to use the MyCSF tool for documenting the self and validated assessments performed for HITRUST certification. HITRUST gives you two options for using the MyCSF tool.
- Purchase A CSF Report – Access for only the assessment (90 days)
- Subscription – Full access year-round for an annual fee
Both will work. Each has its pros and cons. The first option is less expensive; however, you only have access to the tool for 90 days to complete a self-assessment and for your HITRUST External Assessor Organization to complete the validation of your assessment. The subscription option is more expensive, but may be worth it in the long run if you plan to maintain your HITRUST certification on an ongoing basis. The annual subscription allows you to track compliance throughout the year, access your information in the tool at any time, and roll forward the custom control set from CSF, as well as updates into your next year’s assessment.

Step-by-Step HITRUST Certification Process
- Download the CSF Framework: Start by accessing the most recent version of the HITRUST CSF to understand baseline controls.
- Engage a HITRUST Authorized External Assessor: This assessor will guide the process, perform evidence review, and validate scoring.
- Choose an Assessment Level: Align your organization’s risk profile, maturity, and budget with one of the three certification levels.
- Perform a Readiness Assessment: Conduct an internal or assessor-led review to identify control gaps and remediation areas.
- Remediate Gaps: Address deficiencies identified during the readiness phase. Document remediation efforts in MyCSF.
- Conduct Fieldwork: The assessor will evaluate evidence across selected control domains.
- Develop and Approve CAPs: Submit Corrective Action Plans (CAPs) for any partially met or unmet controls.
- Submit to HITRUST: After assessor review, the finalized package is submitted to HITRUST for quality assurance and certification approval.
What Are the Detailed Steps for HITRUST Certification?
We’ve discussed the general steps for the HITRUST assessment and certification journey – but in this section, we will dive into the details of the assessment process, which occurs during the 90-day testing window through final certification.
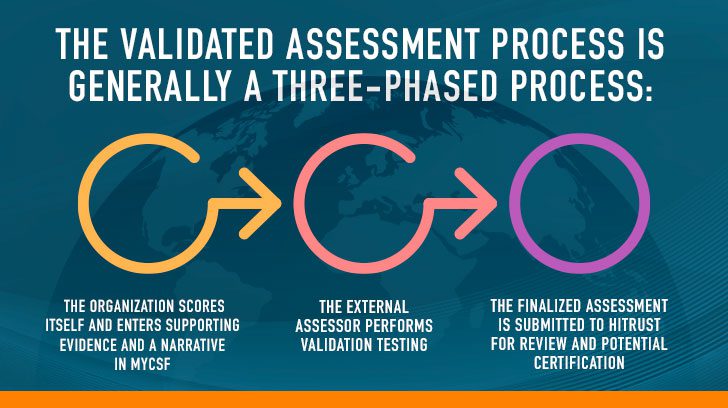
The validated assessment process is generally a three-phased process:
- The organization scores itself and enters supporting evidence and a narrative in MyCSF inheritance requests may also be entered and submitted to service providers.
- The external assessor performs validation testing, which includes evidence reviews and on-site testing if needed.
- The finalized assessment is submitted to HITRUST for review and potential certification.
Step One: Narrative, Self-Scoring, and Evidence Collection
This requires you or a member of your organization to evaluate your compliance with each required control against the one (1) or five (5) maturity levels, depending on the assessment type, as noted:
- Process (r2)
- Procedure (r2)
- Implementation (e1, i1, r2)
- Measure (r2)
- Managed (r2)
Along the way, you will supply certain evidence and a narrative based on guidance and other requests from your assessor. Controls are grouped within 19 different assessment domains. Once you’ve documented your assessment for all of the controls within a domain, you will submit the domain to your Certified CSF Assessor. This portion of the process typically takes four to six weeks for an r2 assessment and much less for an e1/i1 assessment.
Step Two: Assessor Review and Validation Testing, Submission to HITRUST
Upon receiving a submitted domain, the assessor begins validating your self-assessment scoring against the available evidence. Similarly, your assessor will be following HITRUST’s sampling guidance to test the controls against the same maturity levels.
If your assessments agree, the assessor will record the agreement in the tool and document the procedures performed to validate the assessment.
If the assessor disagrees with your self-assessment ratings, the assessor may return a control back to you in the MyCSF tool with comments.
If your assessor performed a readiness assessment (often referred to as a gap assessment) and you’ve addressed all the findings, you will have minimized the likelihood of running into surprises or disagreements between the self and validated assessments. If you skipped the preparation phase and did not perform a thorough self-assessment/readiness assessment or did not adhere to the HITRUST scoring methodology, this could be a very drawn-out, iterative process to come to an agreement. This portion of the process typically takes another four to six weeks for an r2 assessment, and much less for an e1/i1 assessment.
Step Three: HITRUST Review, Quality Assurance, and Certification
Once you and your assessor agree on scores and all evidence has been collected and entered into MyCSF by the assessor, the assessor submits the assessment to HITRUST for review. There are several phases of review and quality assurance (QA) the assessment must go through. First, a basic check for obvious issues (missing comments, missing attachments, etc.) is performed. Following this step, a QA analyst reviews the assessment and may request additional documentation, evidence, or clarification of testing activities, scoping factors or any component of the assessment HITRUST determines requires follow-up prior to issuance of the report and certification letter. This process typically takes anywhere from four to six weeks.

HITRUST Timeline & Cost Considerations
The HITRUST journey can take anywhere from three months (for e1/i1) to a year or more (for r2), depending on your organization’s readiness. Costs vary based on scope and assessment level.
How Much Does It Cost to Become HITRUST Certified?
“How much does HITRUST cost?” This is a very typical question many clients ask during initial conversations. That question leads to a complex answer since there are three primary costs associated with achieving (and maintaining) HITRUST certification. HITRUST should not be considered a one-and-done assessment for the organization, as true compliance with HITRUST requirements requires the integration of a culture of security and compliance within the organization.
Organizations can expect to make three primary investments to achieve and maintain HITRUST certification.
- Fees for access to MyCSF and assessment objects – The fees to access MyCSF and to obtain a validated assessment report (which is required for certification) will range from $20k to $50k+ annually for most organizations.
- HITRUST External Assessor Assessment Fees – These are the fees paid to your assessor firm (your auditor) and they generally range from $40k to $250k+ annually. These fees can vary quite broadly based on the type of assessment (e1/i1/r2, readiness/validated) as well as the scope of the assessment. Any quality assessor firm will be willing to walk you through the scoping process to understand the size and complexity of the environment before quoting a specific price. The fees are most significant in the first year as this typically involves a readiness assessment as well as the first validated assessment, and then fees drop significantly as the organization transitions to the interim assessment and then a fresh validated assessment.
- Internal costs tied to resources, tools, personnel, and capital – Just like a home requires ongoing investment to be designed, built, and maintained, your organization will need to make an investment in the people, processes, and technologies that serve as the structure of your HITRUST compliance program. It is difficult to place a rough figure on this due to variations between organizations, but the organization should be aware these investments will be significant.
How Long is HITRUST Certification Good For?
- e1 Certification: Valid for one year, aligning with most third-party risk management programs that follow an annual cycle for reviewing audit reports and questionnaires.
- i1 Certification: Valid for one year, requiring a full annual assessment similar to SOC 1, SOC 2, PCI, and HIPAA audits. HITRUST now offers a rapid recertification option, allowing qualified entities to re-certify with a reduced set of requirements.
- r2 Certification: Valid for two years, but requires an interim assessment after the first year to confirm remediation of gaps and ongoing program effectiveness. If no issues are found, certification continues until the two-year mark, when a full reassessment is required.
- Interim Assessments: Cover fewer requirements than the initial certification but use the same testing rigor. A full reassessment is required if there are significant changes in size, scope, or systems. Organizations should consult their assessor during planning to avoid surprises.
Control Categories, Objectives & PRISMA Scoring
The HITRUST CSF consists of 14 control categories, 49 control objectives, and 156 control specifications. These are grouped into 19 assessment domains. HITRUST employs the Preferred Reporting Items for Systematic reviews and Meta-Analyses (PRISMA) maturity model for scoring, especially for r2 assessments. r2 assessments require evaluations across all five PRISMA levels (Policy, Procedure, Implemented, Measured, Managed), while e1 and i1 focus mainly on implementation maturity.
How Many Controls Are Required for HITRUST Certification?
Most r2 assessments contain 300-400 requirement statements, with 225 being a typical minimum. The e1 and i1 assessments will include a static number of requirements, with the current e1 containing 44 requirements and the current i1 including 182 requirements. Not all individual requirement statements are mandatory to be compliant for certification, but all requirement statements are evaluated based on scores that are averaged across each of the 19 domains in MyCSF. The AI security assessment adds approximately 44 requirements to its baseline assessment based on a number of scoping factors.
What is the Process for Completing a Validated HITRUST Assessment?
At this point, let’s assume you have performed a self/readiness assessment, remediated any control gaps, obtained access to the MyCSF tool, and engaged a HITRUST Certified CSF Assessor.
One important item to keep in mind is that all testing must be performed within a 90-day window, so organizations should consider resource availability and potential disruptions when planning for the assessment. The assessment process is not complicated in terms of process, but most organizations that struggle do so because of the enormity of the assessment.

Maintaining HITRUST Certification & Interim Requirements
For sustained HITRUST compliance, organizations must actively maintain controls post-certification:
e1 and i1: Annual reassessment is mandatory. i1 supports a rapid recertification model if few control changes exist.
r2: A mid-cycle interim assessment is required, testing at least one control from each domain and evaluating all active CAPs.
Best practices include maintaining a compliance calendar, delegating control ownership across departments, and conducting quarterly self-reviews to catch drift early. Just as any organization must maintain the information security program in terms of policy and procedure reviews, tool configurations, and other activities, it must maintain the overall compliance program to ensure that:
- Controls intended to address specific requirements continue to be appropriate for the organization based on an assessment of risk.
- Controls are effectively implemented and executed as required based on the necessary cadence.
This is especially important for any activities that must be performed at a specific point in time, or on a given cadence, because it is not possible to go back in time and perform some function that was not performed at the proper time.
Organizations should commit to developing and maintaining information security program schedules, implementing a team-based approach to compliance, and leveraging the risk assessment process to aid the organization in managing change. If properly executed, the organization will be able to maintain an effective information security program that continually improves the security posture of the organization, as well as maintains a strong level of compliance as a byproduct of security.
Is an Authorized CSF Assessor Required for HITRUST?
Yes! To achieve HITRUST certification, an organization is required to work with an External Assessor Organization that has been vetted and approved by HITRUST to perform validated assessments. At an organizational level, there are requirements around background, training, and certification of individual assessors.
To serve our clients as an external assessor organization, we maintain a staff of experienced and qualified assessors who are certified by HITRUST. Our HITRUST assessors complete annual training activities and hold industry licenses and certifications, including the CCSFP, CHQP, CISA, CISSP, CPA, and others.
Understanding Your HITRUST Certification Journey
We hope this has helped you understand the process of obtaining a HITRUST certification. The HITRUST process can be lengthy and requires preparation and planning. However, it can provide your clients and partners peace of mind knowing your organization has taken the steps necessary to protect the sensitive data in your possession.
As Linford & Co is a HITRUST External Assessor Organization, we would be happy to assist you with any of your HITRUST compliance needs. Please contact us to arrange a consultation or with any additional questions you may have about our HITRUST Assessment & Certification services.
This article was originally published on 1/3/2018 and was updated on 9/24/2025.









