The National Institute of Standards and Technology (NIST) defines Information Security Continuous Monitoring (ISCM) as : “maintaining ongoing awareness of information security, vulnerabilities, and threats to support organizational risk management decisions.” In other words, an information security methodology that ensures the effectiveness of security controls related to systems and networks, by constantly assessing their implementation and organizational security status.
NIST continuous monitoring isn’t just about automated watchdogs, though—among other things, it requires a reporting structure designed to make real-time, data-driven risk management decisions in accordance with organizational risk tolerance. And just as the current threat landscape is dynamic, your security program must be equally dynamic.
The Benefits of Continuous Security Monitoring
The increased visibility provided by continuous monitoring leads to a better understanding of an organization’s security posture and the effectiveness of their security program. This includes accelerated and targeted responses to data breach attempts and infrastructure space concerns, enabling a lower meant-time-to-resolution (MTTR), which is a key performance metric for most SaaS, PaaS, and IaaS companies.
Runbooks can be integrated to guide automated resolution, saving the company time, cost, and potential human error in resolution. Mining system logs allows the creation of accurate performance, security, and user behavior benchmarks, further strengthening the identification of and best response to intrusions and malware.
And, of course, retaining customer trust by not being in the news for a security breach is always good for business.
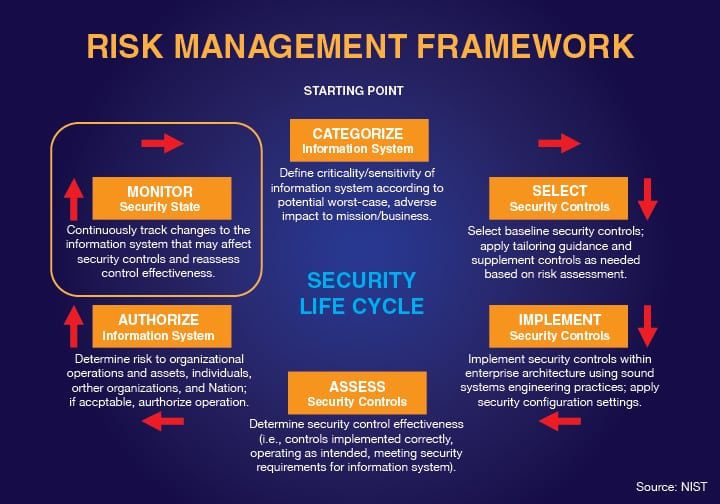
The Continuous Monitoring Process
To establish, implement, and maintain information security continuous monitoring, an organization must:
- Define an ISCM strategy.
- Establish an ISCM program.
- Implement an ISCM program.
- Analyze data.
- Report findings.
- Respond to findings.
- Review and update the ISCM strategy and program.
While there is no single right way to implement continuous monitoring, the general process requires automation tools that monitor and log defined events.
In addition to gathering data, automation is used to compile and analyze it, creating reports whose data is used to drive strategic responses to events. From an organizational standpoint, processes and reporting structures can be adapted as necessary to create better efficiencies.
The continuous monitoring process is designed to detect control failure and overall effectiveness of the controls, as part of the information security continuous monitoring strategy to “ensure the continued effectiveness of security controls.” Thus, a robust and continuously updated ISCM program opens the way to more effective security controls.
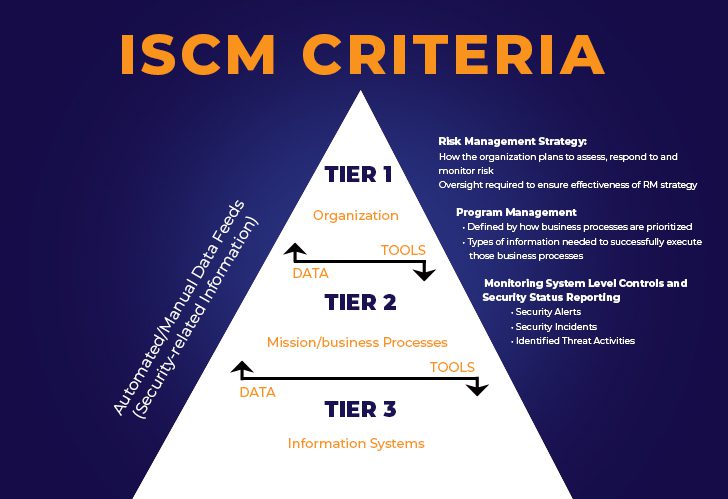
Defining and Implementing an ISCM Strategy
The overall goal of successful continuous monitoring is greater data security resilience and greater compliance with specific certification standards, such as FedRAMP continuous monitoring.
To start, the monitoring profile must align with your organizational and technical constraints. For any continuous monitoring program to be successful, you must know your enterprise. Pick monitoring targets strategically—more systems can be added once you’ve established a good baseline.
This requires conversations with relevant teams’ stakeholders regarding the IT environment, their needs, and the company’s cost limitations. At this point, the highest priority is any critical, unmonitored system going offline as a result of an intrusion attempt or spike in network activity.
The organizational management is responsible for identifying risks to the organization and defining the approach to address those risks. The organizational risk appetite defines the levels of risk that senior management is willing to take in order to meet their stated strategic objectives. Then people, policies, processes, and technology are leveraged to buy down the risks facing the organization, starting in the highest-risk areas and moving toward the lower-risk areas.
After the critical systems, the next priority is the most important metrics. This can range from application errors to performance-related events, capturing firewall configuration change events or blocked traffic details to focusing on capacity-related server problems.
As part of your continuous monitoring strategy, focus on both proactive and detective techniques. Proactive techniques include active vulnerability scanning, configuration, and patch management, as well as monitoring your applications and endpoints. Detective techniques include log consolidation, reduction, analysis and reporting, and other alerting mechanisms.
Once you know what must be monitored, the next step is deciding what systems and tools to use in order to analyze the data.
Cyber Security Continuous Monitoring Systems & Tools
When deciding what system to utilize for continuous monitoring, prioritize ones that will fit your existing environment and as much as possible of your predicted future environment. This means a chosen system must:
- Work with the identified critical application stacks, including software components, infrastructure, and network.
- Easily ingest the logs, metrics, and events of each integration point in the application stacks.
- Correlate different events and metrics from the same application stack touchpoints.
- Be able to store and process the volume of data gathered over time. Better still if it can analyze and report these at set intervals.
- Enable search and visualization of the collected information.
- Include alert communication functionality if a set trigger is met, such as trends or anomalies.
- Encrypt data captured from the stacks both at rest and in transit, including masking sensitive data.
- Comply with industry regulations and mandates with respect to the geographical location of these logs.
An ideal, but not required, aspect is full support from the continuous monitoring system developer. The process requires ongoing, iterative management, so you should be able to readily communicate with the company that designed the solution.
Although an automated system provides the means by which to gather and analyze data, send communications, and maintain logs, the human aspect should never be ignored. Relevant teams should be involved in alerts and remediation efforts, as well as providing feedback and conducting continuous penetration testing.
One thing to be cautious about is getting lost in the volumes of data that are produced. If something isn’t working, make the needed changes so that it does. The tools must provide the data to identify areas where remediation is necessary and risk decisions are supported.
Then there’s the iteration phase of continuous monitoring. Evaluate if an implemented solution is providing the correct data and facilitating decision-making regarding organizational risks. As your awareness increases, you’ll be able to prioritize your remediation efforts.
Reviewing and Responding to Findings
Once data has been collected and analyzed, your organization can respond to any identified gaps. This may include implementing new security controls or expanding the range of existing controls. Documentation of remediation efforts is required, and a critical element of updating the ISCM program.
Ultimately, leadership and stakeholders must meet regularly to review automated reports and findings, assess gaps or new threats to security, and improve the organization’s security posture.
Personal Guidance for Continuous Monitoring
If you’d like more personal guidance on implementing or improving your continuous monitoring process, please contact us.
This article was originally published on 5/26/2016 and was updated on 8/13/24.









