Containers, and the concept of containerization, have been continuing to grow. Many organizations are struggling to keep up with the new technology and keep their systems secure. If you and your organization are considering trying to use or moving to containers, many of your current security processes and procedures will no longer work with containerization or will require some updates.
A high-level description of containers and some instructions on how to secure them is as follows. If you would like more information, please feel free to reach out, and we can help walk you through what is needed to meet your compliance goals and move into the world of containers.
What are Containers? What is Containerization?
As you read articles and attend conferences, you may hear a lot about the “new” wave of “virtualization” called containers. Containers allow you to run an application and all of its dependencies in isolated processes. The goal of containerization is to allow you to easily package everything you need to run your software reliably when moved from one environment to another.
What Does Containerization Do?
Containers help support continuous integration and also increase consistency, efficiency, productivity, and version control. Some of the biggest names in containerization these days are Docker and Kubernetes, but many additional companies have started offering containerization services, including Google, Amazon, Red Hat, etc. To help standardize runtime and formats, the Open Container Initiative (OCI) was created in 2015 by Docker and others, and currently contains two specifications: the Runtime Specification (runtime-spec) and the Image Specification (image-spec).
What Are the Benefits of Containerization?
There are a number of benefits that moving to containerization provides. Some of the main benefits companies can see include:
- Increased Portability
- Simple and Fast Deployment
- Enhanced Productivity
- Reduced Cost
- Improved Scalability
- Reduced Attack Surface
What is the Difference Between Virtual Machines and Containers?
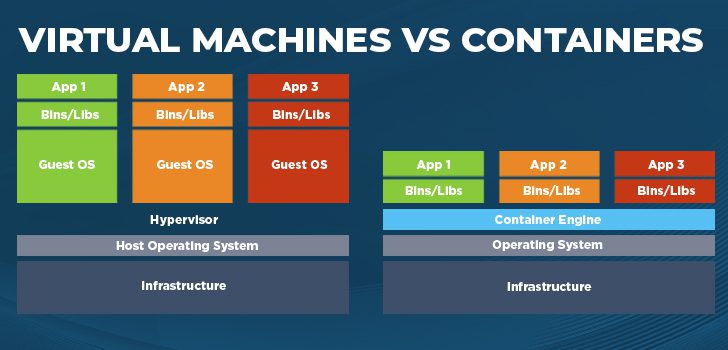
Virtual machines (VMs) package an entire operating system, including application code and associated dependencies, together into a virtual disk image. A hypervisor is then used to manage and run the VM. VMs are therefore larger in size and can be more resource-intensive to operate since each guest VM requires its own dedicated memory, disk space, etc. Containers are different as they only contain the software, libraries, and other dependencies required to run a specific application or service, and they then run directly on an operating system without requiring their own operating system instance. This allows you to eliminate unneeded software, leaving a small and efficient “container” holding your application. It also allows you to have many more instances running the same hardware as before when using VMs.
What is Containerization Security?
Containerization security is the approach an organization can take to ensure that its containers are secure from unwanted threats and risks. An organization needs to implement and follow effective security strategies to have success with containerization. Read on for additional information on securing and monitoring your containers.
What is the Major Security Concern with Containers?
If you decide to move in the direction of containerization, keep in mind that the traditional security model is no longer valid and you may have to redesign how you approach compliance and security. For example, many of your current security tools are host-based, and when you remove the dependency of the host you are probably now in the market for new tools.
One major security concern is that containerization lacks isolation from the host OS. So if there is a vulnerability with the host kernel/OS, it could impact all containers. Luckily, security tools allow organizations to automate a lot of the security that they rely upon in a virtual or bare metal approach.

How Secure are Containers? How to Secure and Monitor Containers for Security Compliance
Because of their different nature, securing and monitoring containers requires a different approach from traditional servers or VMs. Some compliance considerations are provided below.
Overall Security and Hardening
A good starting point to determine security controls and guidance is to utilize the vendor-provided security benchmark or hardening guidelines. For example, the Center for Internet Security created a CIS Docker Community Edition Benchmark. This document walks through steps on host configuration, daemon configuration, daemon configuration files, container images, runtime, etc. There are also a lot of supporting GitHub repositories to help with security configuration.
Monitoring
Monitoring containers is different from monitoring VMs in that you do not have traditional tools like host-based firewalls, anti-malware, antivirus, etc. to support the detection of malicious activity within the container. However, a number of vendors provide tools to monitor the availability and security of containers and the underlying host.
You should also add additional monitoring into the SDLC process and monitor, document, and test the image registries and containers. Knowing what each container includes down to the libraries is key to understanding what the threats and vulnerabilities are.
Of course, auditing is always recommended. Monitoring events at the host OS level, the application, and the container daemon level is necessary as well. Depending on your approach and architecture, logs are key to determining gaps in security, especially if you are rebuilding the instances repeatedly, as that instance will not be around for triage and you may not notice the issue until the instance is already rebuilt.
Vulnerability Assessments
In addition to monitoring and general organizational risk management, defining a proper vulnerability assessment process is also key. Luckily, most commercial vulnerability scanners offer some sort of container security scanning to help identify known vulnerabilities and security configuration issues. Be sure to activate these features or search out new tools if your current product does not support containers.
Patching and Hardening
Patching is a bit different in a containerized environment. In the past, you would just update your instances through a manifest, recipe, or other patch management process or tool. With containers, there are two components: the base and the application image. You have to first update the base image and then rebuild the application image. This will force a more complex patching process and more interaction between infrastructure support and development as both are now more closely connected.
Integrity
As a way to enhance the security of containers, Docker (Docker Content Trust) and other container systems have incorporated a signing infrastructure to allow administrators or authorized users to sign container images which helps prevent untrusted or unapproved containers from being deployed.
Isolation/Separation/Access
This is an important consideration, as moving to containers removes the isolation that is available when using VMs since containers share the same kernel. Understanding your requirements both internally and externally will drive your approach on how to limit the risks. One approach some organizations are utilizing is to run the containers from an operating system on a VM. This way if the container or VM is attacked, the compromise is limited to the VM and not the physical host (in some cases the hypervisor) which protects any other VMs or systems that are also present on the physical host.
You can limit the risk of privileged escalation and other security attacks by following the hardening guidelines documented above, and other techniques like using control groups, making sure to run the containers as an unprivileged user, and using namespaces.
Incident Response
As discussed above in monitoring, when you move to containers, you can reduce your ability to perform forensics since the instance or host could have been replaced already. Reviewing all Incident Management and Response processes specifically for containers is important.
Key Takeaways for Containerization Security Implementation
Whether you are thinking about or have moved into the world of containers, security needs to be reevaluated as the standard practices may require augmentation compared to traditional VMs and bare metal servers. We recommend implementing containers in a non-compliance or non-production environment first to try and get a good feel for how to monitor, secure, and support them.
Moving to containers does not mean you cannot get a specific certification or pass an audit or examination, it just means you may need to change some of your security processes. Any large changes like this should also be discussed with your auditor to determine the impact on your compliance requirements.
Linford & Company has extensive experience providing various audits, including SOC 1 Audits, SOC 2 Audits, ISO compliance assessments, and more. If you are interested in learning more about any of our services, please contact us to schedule a free consultation.
This article was originally published on 8/28/2019 and was updated on 1/29/2025.

Tim Nackos joined Linford & Company, LLP in 2022. The first 5 years of his career were spent at the “Big Four” firms EY and KPMG providing IT assurance and advisory services. He also spent 10 years at two large financial institutions primarily in internal audit performing data analytics. Tim is a certified public accountant (CPA) in the state of Utah and is a certified information systems auditor (CISA). He holds both a Master of Accountancy and a Bachelor of Science degree in Accounting from Brigham Young University.




