Our firm has been a HITRUST External Assessor Organization since 2017, and in that time we have successfully helped dozens of organizations obtain and maintain HITRUST certifications. We have identified common pitfalls and other barriers to success and we’ve also learned some keys to success. In this article, I’ll break down some of the most basic information about HITRUST, what HITRUST certification is, and the HITRUST certification process.
What is HITRUST & Why Was It Created?
HITRUST was founded in 2007 as a not-for-profit, initially to develop and champion programs to safeguard sensitive information such as electronically protected health information (ePHI). HITRUST attempts to fill a void that some regulations, such as HIPAA, do not address. Over time, HITRUST has expanded its services and capabilities to support organizations as they manage information risk for global organizations across all industries and throughout the third-party supply chain – it’s still a common misbelief that HITRUST is only for organizations in the healthcare industry.
What is the HITRUST CSF?
The HITRUST has established the HITRUST CSF, which can be used by all organizations that create, access, store, or exchange sensitive and/or regulated data. The CSF includes a prescriptive set of requirements that seek to harmonize the requirements of multiple regulations and standards including ISO, NIST, PCI, HIPAA, CMMC, and many others.
What Does CSF Stand for in HITRUST CSF?
CSF stands for “Common Security Framework”, and it is the foundation of all HITRUST programs and services. The HITRUST CSF standardizes requirements from a broad variety of different information security frameworks, including legal and regulatory requirements, by providing clarity and consistency, and by reducing the burden of compliance. The CSF permits the delivery of HITRUST’s goal to facilitate the delivery of multiple compliance reports based on a single assessment.
Why is HITRUST Important?
HITRUST is important as an organization because it solves an industry-wide challenge: Providing certifiable assurance of information security program operating effectiveness and maturity. There are many information security frameworks and assessment methodologies. Most do not result in a formal certification, and most also do not utilize a maturity assessment model to allow consumers of the certification or report to evaluate the maturity of the organization’s security practices. To understand why a HITRUST certification is accepted so broadly and is considered a gold standard in the industry, download this overview document from HITRUST.
Tip: HITRUST offers a variety of programs for smaller firms as well as startup or venture-backed organizations which can help reduce the costs associated with getting started with HITRUST.
What Are the Benefits of HITRUST Certification?
HITRUST certification offers numerous benefits to organizations across industries. Primarily, it provides a high level of assurance to customers, partners, and stakeholders that the certified organization meets rigorous standards in safeguarding sensitive information, enhancing trust and competitiveness.
In addition, HITRUST certification helps organizations stand out as trusted business partners within the industry. This is thanks to the high standards of the assurance process that supports a set of standard baselines that can be applied equally, as opposed to the quality of more traditional audits, which can vary based on the individual firm conducting the audit. All HITRUST certifications, regardless of assessment type, follow the same rigorous assurance process. Lastly, the HITRUST certification process helps organizations understand how effectively risk-mitigation controls have been applied in the environment, leading to improvement over time.
What is ‘HITRUST Certified’?
Put simply, HITRUST Certified organizations demonstrate compliance with a prescriptive set of requirements at a prescribed level of maturity in a manner intended to provide a given level of assurance depending on the level of certification desired.
Under the HITRUST CSF® Assurance Program Requirements, “HITRUST CSF Certified’ refers to an organization that has met all CSF certification requirements as defined by HITRUST based on industry input and analysis. ‘CSF Certification’ involves performance of a validated assessment leveraging the MyCSFtool, the embedded HITRUST CSF control requirement statements, and the PRISMA maturity model. CSF certification provides relying entities with greater assurance that an assessed entity is appropriately managing risk. CSF certification is designed to remove the variability in acceptable security and privacy requirements by establishing a baseline defined by industry, removing unnecessary and costly negotiations and risk acceptance.”
The Evolution of HITRUST Assessments & Certifications
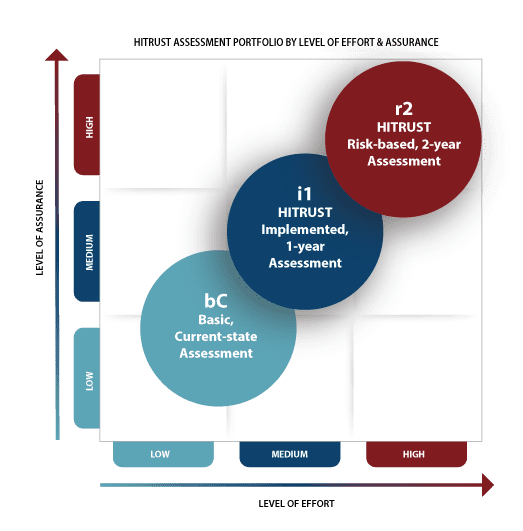
Over the past two years, HITRUST unveiled revisions to the assessment and certification portfolio for HITRUST. Instead of simply providing one level of assessment and certification, there are now three unique levels of assessment and potential certifications each intended to require increasing levels of assurance to support various risk environments.
The HITRUST Essentials, 1-Year (e1) Assessment addresses foundational cybersecurity practices, provides entry-level assurance focused on the most critical cybersecurity controls, and demonstrates that essential cybersecurity hygiene is in place.
The HITRUST Implemented, 1-year (i1) Assessment addresses leading practices, provides a moderate level of assurance that addresses cybersecurity leading practices, and a broader range of active cyber threats than the e1 assessment.
The HITRUST Risk-based, 2-year (r2) Assessment addresses expanded practices and provides a high level of assurance that focuses on a comprehensive risk-based specification of controls with an expanded approach to risk management and compliance evaluation.
All three of these assessments can lead to the related form of HITRUST certification through the execution of a validated assessment and assurance review by HITRUST.
Image source: HITRUST
What Are the HITRUST Certification Requirements?
To achieve any HITRUST certification, the organization must exceed baseline scores for certification for requirements that are distributed across various domains. HITRUST scoping is more complex for the r2 assessment due to the usage of five different levels of maturity vs. one level of maturity for the e1 and i1 assessments.
What Types of HITRUST Assessments Are There?
There are multiple HITRUST assessment types, each aligning with a particular end result for the entity undergoing the assessment. For organizations wishing to establish an understanding of current levels of compliance compared with a desired future state, the readiness assessment is valuable. The self-assessment is appropriate for an organization wishing to complete an assessment leveraging internal resources but not submitting the assessment for potential certification. For organizations wishing to become HITRUST certified, the validated assessment, which requires the involvement of an authorized external assessor, is appropriate.
HITRUST Readiness Assessment
A readiness assessment is designed to evaluate an organization’s readiness to successfully obtain HITRUST certification. This assessment may or may not be done through the MyCSF tool, and in lieu of a formal HITRUST report being issued, a list of gaps and remediation guidance is produced and provided to guide the client through the remediation process in preparation for an assessment.
HITRUST Self-Assessment
Organizations may choose to perform a self-assessment against the applicable CSF requirements within the myCSF tool. HITRUST will also perform a limited validation of the self-assessment results that can be shared with a relying user entity. We have seen organizations get good value from a self-assessment when they have the appropriate skills and expertise as well as score themselves fairly without bias. We have had a few clients perform a self-assessment and score themselves with perfect scores without providing sufficient support for us to come to the same conclusions. It pays to be hard on yourself during the self-assessment, especially to avoid these potential HITRUST readiness assessment pitfalls. It’s important to note a self-assessment does not result in certification. If certification is the goal, a validated assessment is required.
HITRUST Validated Assessment
A validated assessment must be performed by a HITRUST assessor firm. A validated assessment requires an authorized external assessor to assess compliance with the applicable HITRUST CSF requirements. A validated assessment must be performed for an organization to become certified by HITRUST. Upon completion of a validated assessment, an organization can pay a HITRUST certification fee, submit any corrective action plans specific to the HITRUST assessment findings, and have HITRUST spot-check the results of the validated assessment. If no significant issues are identified beyond what was identified in the validated assessment, an organization will receive a HITRUST certification and certification letter.
What is HITRUST MyCSF?
As mentioned above, access to the HITRUST CSF is free. The MyCSF tool, on the other hand, is a SaaS platform that allows organizations to navigate the HITRUST assessment process. It includes functions to allow the scoping and execution of the engagement, which includes the development of narrative responses, the linking of evidence to items, and scoring capabilities along with other advanced functions including powerful analytics and reporting capabilities.
Can MyCSF Replace My Current GRC Platform?
We often get this question – we have found that most organizations do not use MyCSF as its formal system of record for GRC purposes. MyCSF does offer some GRC capabilities, but most organizations leverage the features of a full-functioned GRC to supplement MyCSF usage. This is one reason why MyCSF supports integration with major GRC platforms and the HITRUST Assessment XChange.
How is MyCSF used for Assessment & Certification?
HITRUST certification and assessment are actually performed against a subset of the HITRUST CSF and the size of the assessment depends on the desired certification and potentially, scoping factors. If the organization wishes to undergo a formal HITRUST assessment, access to MyCSF is required. Access to MyCSF is offered on both a subscription model as well as a one-time assessment model. In our experience, most clients choose to obtain the subscription model as it offers two distinct advantages over the one-time-assessment model:
- Reduced assessment management costs: With a HITRUST MyCSF subscription, an organization can save both time and money by maintaining data and Corrective Action Plans (CAPs) from assessments, significantly reducing data entry by internal and external resources when performing future assessments. Without this, each assessment becomes a standalone activity and there is significant repetition of work between assessments.
- Continuous real-time visibility of compliance stature: For more mature organizations that desire to move to a continuous monitoring methodology, the MyCSF tool can be leveraged to provide visibility into the organization’s risk posture throughout the assessment lifecycle.
While scoping factors are not applicable to the e1 or i1 assessments, for organizations pursuing certification of an r2 assessment, access to MyCSF is also required to determine the size of the assessment due to scoping factors. If your organization does not already have access to MyCSF, you can work with one of our assessors to scope the size and complexity of your assessment before you commit to the purchase of MyCSF access. We can also share insights into the various subscription options available.
How Much Does the HITRUST CSF Cost?
It is important to understand that access to the HITRUST CSF is free of charge. Anyone may download the HITRUST CSF and utilize it within their own organization to achieve a number of other goals aside from formal certification. For example, the HITRUST CSF is an excellent tool for understanding how various information security frameworks correlate or “map” to one another.
HITRUST Certification Costs
HITRUST compliance and certification costs vary by the type of assessment and whether certification is desired. For perspective, many of our SOC 2 clients have 80-100 controls tested within a SOC 2 report. Currently, an e1 assessment contains 44 requirements, and an i1 validated assessment includes 182 specific requirements (as of CSF v11). A typical r2 validated assessment may have upwards of 350+ control requirements and scoping of the assessment is required to determine level of effort.
For an e1 or i1 assessment, both of which are implementation-focused, the assessor will only assess the implementation of controls, so those 44 or 182 requirements will be assessed for implementation only.
However, requirements in an r2 validated assessment are assessed for three to five different maturity levels. That could mean an assessor has to look at 1,500 or more pieces of documentation or evidence to complete a validated assessment. Another reason for the higher fees is that assessor firms must pay an annual fee to HITRUST each year to maintain their assessor status.
Fees for the e1, i1, and r2 validated assessments range from $20,000/yr to $250,000/yr depending on the factors associated with the assessment. A quality external assessor firm will want to go through a basic scoping process to understand the scope of the assessment before issuing a formal quote.
HITRUST Implementation Levels
Each of the controls defined by HITRUST has three different implementation levels associated with them. The implementation levels build off of each other. This means a Level 3 implementation includes all of the Level 1 and Level 2 implementations as well. Implementation levels are built upon three unique risk factors:
- Organization factors: e.g., the type of organization or the size of the organization.
- System factors: e.g., internet connections, number of records, or the use of mobile devices in the organization.
- Regulatory factors: e.g., state or specialized industry requirements.
These levels are only relevant to r2 validated assessments since the e1 and i1 assessments do not leverage scoping factors to tailor the assessment to the organization’s risk profile.
What Are the HITRUST Domains?
It’s important to understand how the hierarchy of requirements works within a HITRUST assessment.
Domains
The HITRUST CSF starts out at the domain level, which are major practice areas within information security and regulatory compliance. Examples of domains are Endpoint Protection, Information Security Risk Management, and Data Protection & Privacy.
Control Families
Controls are broken down from the domain level into control families. These can be thought of as a group of controls that may be spread across multiple domains. They are also commonly referred to as control objectives.
Requirement Statements
Requirement statements are the most detailed level of control assessment and are where evidence is obtained to assess the maturity of the organization’s operation of controls to address the requirement, which may vary in depth and detail based on the HITRUST implementation levels addressed above.
What is a HITRUST Control?
It’s important to understand there are some vernacular differences between HITRUST and the rest of the information security industry. Where the industry tends to focus on controls, HITRUST focuses on requirements in lieu of what we typically call controls.
Per HITRUST, a control objective is the desired outcome of the successful implementation and operation of a control. HITRUST requirements are the activities, performed according to HITRUST specifications that will result in the effective operation of a control and achievement of the control objective. I’ll break this down:
- Control Objective: The organization ensures organizational personnel are qualified to perform assigned duties in the areas of information security and incident response.
- Control: Background checks, education verification, and reference checking will be used to perform screening activities.
- Requirement: Perform background screening and assess risk for all personnel prior to the start of employment.
Maturity Levels & Scoring
Scoring for the e1 and i1 assessments is relatively simple. For an e1 or i1 Validated Assessment to result in certification, no assessment domain’s straight-average score can be lower than 83% when considering only the “implementation” score associated with a given requirement and the evaluative elements associated with it.
However, scoring in an r2 assessment is much more complicated.
To receive certification following an r2 validated assessment, you must have at least a score of 62% (HITRUST 3-) or greater in each domain with corrective action plans for any requirements scoring less than 62%. One key lesson we have learned is that if it is your organization’s first time through HITRUST, you might consider focusing on policy, procedure, and implementation scores as opposed to measured and managed scores. Identifying metrics related to certain processes can be difficult at times. If you have a 75% score without evidence of measured and managed, you are meeting the HITRUST requirement.
When organizations hold themselves out as HITRUST certified, they don’t typically offer the score from the Validated assessment. As a result, ask yourself if it’s worth the additional effort to go after a few extra points. That same time could be focused on documenting policies and procedures that are not in place and implementing required controls. Remember that a perfect policy, procedure, and implementation score gets you 75% which does not even require a corrective action plan for a requirement.
The following illustration shows the maximum points available for each HITRUST maturity level when undergoing an r2 assessment.
- Policy – 15%
- Procedure – 20%
- Implemented – 40%
- Measured – 10%
- Managed – 15%
HITRUST scoring is a complex topic. For a more in-depth breakdown, take a look at How to Score HITRUST CSF Controls.
What is HITRUST Inheritance?
HITRUST inheritance, also known as the Shared Responsibility Model, is valuable to organizations utilizing services from other HITRUST-certified entities. For example, if your organization is planning to obtain HITRUST certification for a SaaS platform that is hosted in AWS the organization can significantly reduce the number of requirements it is responsible for during the assessment.
The inheritance process is simple to navigate and is one of the first activities performed during the assessment. In some cases, the requirement is inherited at a rate of 100%, which means no responsibility lies with the client organization. In other cases, the requirement may be inherited at 50% which means even though the cloud service provider may be partially responsible for a requirement, the client organization must still address their compliance with that requirement during an assessment.
Why Do Organizations Need HITRUST Certification?
The request for HITRUST certification by a key client or business partner is typically sufficient motivation for any organization. However, we strongly suggest organizations consider the options available to them as HITRUST certification is a significant investment in both time, resources, and capital, and should not be taken lightly. The e1 or i1 assessments are an excellent starting point for organizations that desire to obtain HITRUST certification but do not require the higher level of assurance the r2 assessment and certification provide.
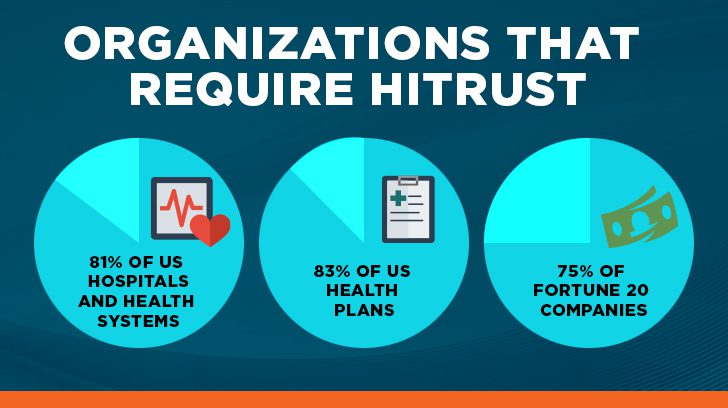
What Types of Organizations Require HITRUST?
HITRUST has experienced significant levels of adoption within the healthcare industry, not only in the United States but also internationally. Per HITRUST’s measurements, 81% of US hospitals and health systems, 83% of US health plans, and 75% of Fortune 20 Companies have adopted HITRUST assessments and certifications internally or as part of their third-party risk management processes.
Who Should Pursue HITRUST Certification?
The most common advice we give to our clients is that if there is a sufficient business justification to warrant HITRUST certification, then starting with a readiness assessment is the best way to set the organization up for a successful validated assessment. We know HITRUST compliance and certification is a major investment and requires significant resources to be successful. Our auditors are happy to talk through the selection criteria and help navigate discussions our clients may have with their customers when HITRUST certification is requested.
Historically, SOC 2 was used as a stepping stone to get an organization into the “compliance mindset”. More recently, the e1 Validated Assessment with Certification has become a de facto starting point that is accessible to most organizations just getting started on their HITRUST journey.
In addition to the e1 or even the i1, there are other options or audits that a business may use to evidence its control environment used to secure sensitive data. Read here to learn more about the differences between SOC 2 and HITRUST. As an alternative to the e1 or i1, SOC 2 is an excellent primer to get an organization used to the policy and implementation requirements which are greatly expanded for HITRUST. Think of it as training wheels. If SOC 2 is an option, then consider starting with SOC 2 before initiating HITRUST, or consider the benefits of both.
What Does HITRUST Certification Mean For My Organization?
HITRUST certification means that the organization has undergone a thorough assessment of the information security program focused around a given scope which is generally limited to one or more implemented systems. Generally, an organization does not pursue HITRUST certification for the entire organization, as the application of stringent information security requirements across the board is inefficient from a risk and resource allocation perspective.
The achievement of HITRUST certification requires:
- Satisfactory completion of a HITRUST-validated assessment by an external assessor firm such as Linford & Company.
- Validation of the quality and accuracy of the assessment by HITRUST through the HITRUST assurance program.
How Is HITRUST Based on Other Frameworks?
The CSF is structured based on ISO/IEC 27001 and 27002 standards and also encompasses over 40 other security and privacy regulations, standards, and frameworks, providing comprehensive coverage. HITRUST maintains a threat-adaptive approach and works to harmonize existing sources, incorporating new or modified sources when necessary. With each release of the CSF, HITRUST integrates and normalizes requirements and best practices while eliminating redundancy within the framework.
For comparisons of common frameworks and regulations covered by the HITRUST CSF, see:
- What is ISO Security Standards and Professional Practice of Internal Auditing
- Understanding the NIST Privacy Framework
- SOC 2 Security vs. ISO 27001 Certification
Are you trying to compare HITRUST to other assessment frameworks in the cybersecurity space? If so, read this whitepaper comparing the CSF, ISO 27001, and NIST 800-53.
What is the Difference Between HIPAA & HITRUST?
HITRUST has its roots in HIPAA compliance and has grown to be a very useful mechanism for validating HIPAA compliance, but the modern implementation of HITRUST goes well beyond the healthcare industry. To learn more about HIPAA and HITRUST, check out some of our related articles:
- HIPAA Gap Analysis: Critical & Recent Compliance Gaps You Need to Know
- A Summarized Guide to HIPAA Compliance Audits
- HITRUST vs HIPAA: Understanding The Benefits of HITRUST Certification
HITRUST Lessons Learned: Keys to Success
To summarize, here are some tips to make for a smoother adoption of HITRUST:
- When you do scope the coverage of your e1, i1, or r2 assessment, do so wisely and cover only the services that are most relevant to the user entities that are demanding HITRUST certification.
- Leverage SOC 2 when possible – consider using SOC 2 as a starting point in your journey to HITRUST compliance, and explore whether the e1 or i1 assessment is an appropriate step in your HITRUST journey, if the r2 certification is your intended goal.
- Perform a thorough self-assessment and identify specific evidence to support scores.
- Consider leaving out measured and managed scoring and evidence for the first year. Focus on the policy, procedure, and implementation of maturity levels since those combine for the majority of the score for each requirement (75%).
- Know your resources and have resources available to remediate both policy and procedural gaps, as well as implementation gaps. Although the e1 and i1 assessments are implementation-focused, there are many requirements associated with policy and procedure documentation.
Also, please contact us with any HITRUST-related questions. We are happy to consult about providing a HITRUST assessment for your organization.
This article was originally published on 5/25/2022 and was updated on 10/4/2023.

Richard Rieben is a Partner and HITRUST practice lead at Linford & Co., where he leads audits and assessments covering various frameworks including HITRUST, SOC, CMMC, and NIST. With over 20 years of experience in IT and cybersecurity and various certifications including PMP, CISSP, CCSFP, GSNA, and CASP+, Richard is skilled in helping growing organizations achieve their information security and compliance goals. He holds a Bachelor of Science in Business Management and an MBA from Western Governors University.